B83%
Quality Score
7
Pages
124
Issues
8.0
Avg Confidence
7.9
Avg Priority
51 Critical54 High18 Medium1 Low

>_ Testers.AI
AI Analysis
Create.Xyz was tested and 124 issues were detected across the site. The most critical finding was: Third-Party Tracking Script Loaded Without Confirmed User Consent. Issues span Security, Performance, A11y, Other categories. Persona feedback rated Visual highest (7/10) and Accessibility lowest (6/10).
Qualitative Quality
Create.Xyz
Category Avg
Best in Category
Pages Tested · 7 screenshots

Homepage

create.xyz
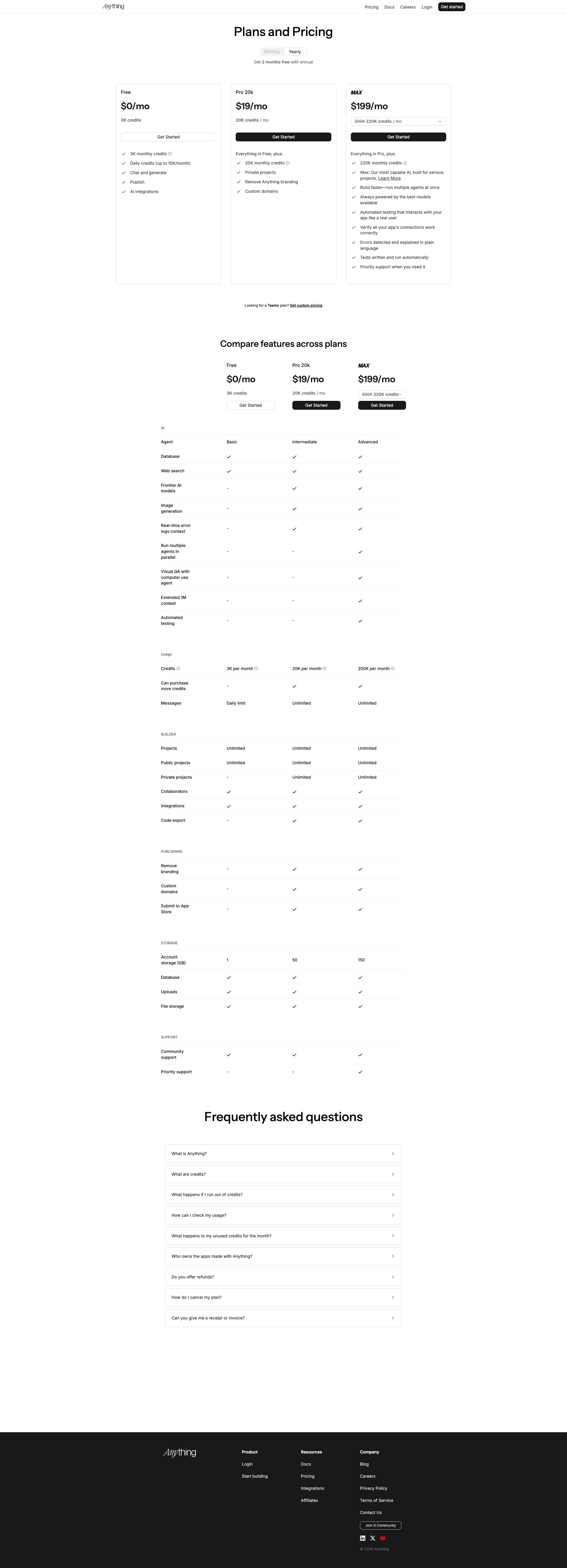
create.xyz

create.xyz

create.xyz
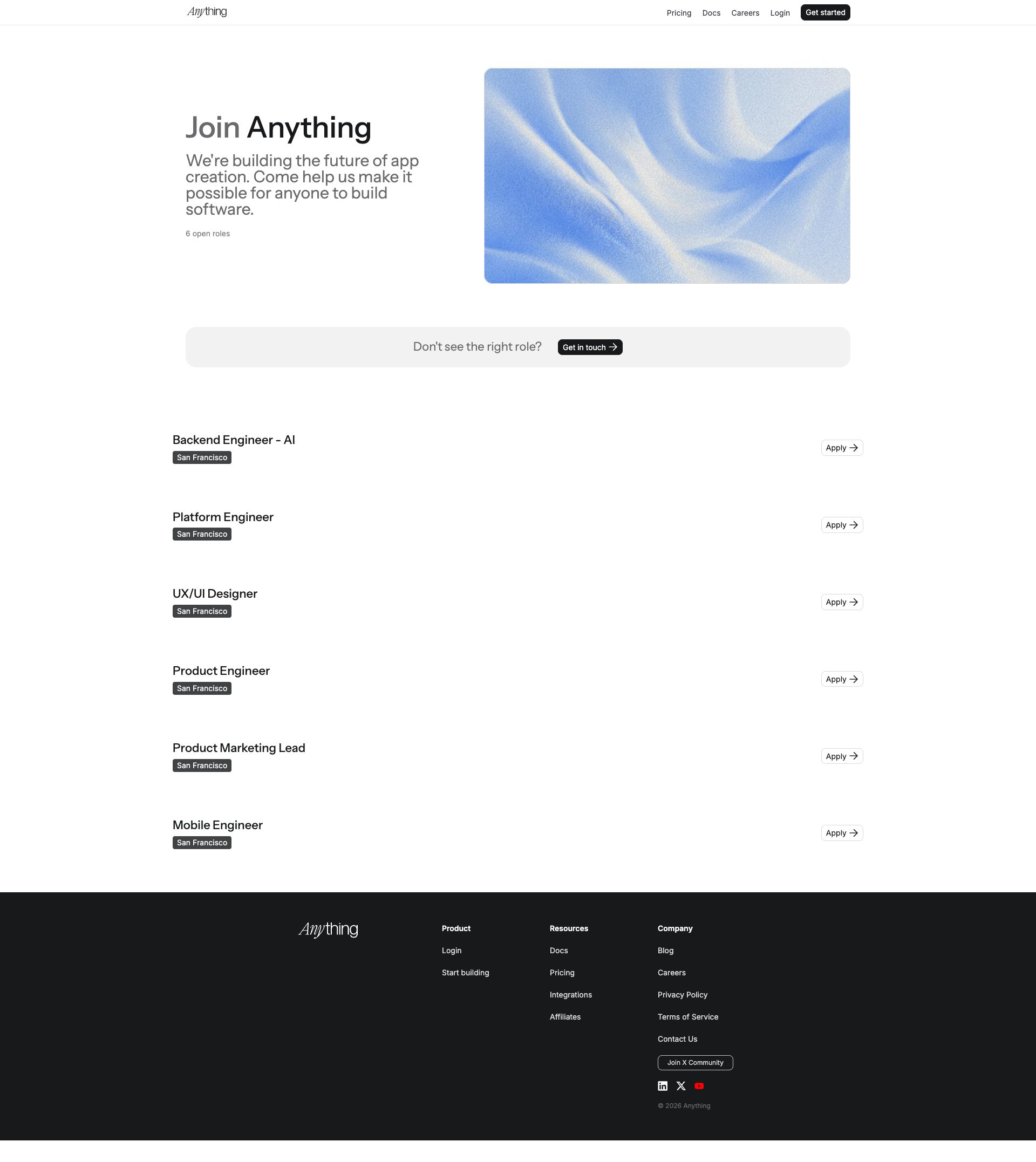
create.xyz
create.xyz
Detected Issues · 124 total
1
Third-Party Tracking Script Loaded Without Confirmed User Consent
CRIT P9
Prompt to Fix
Identify all third-party scripts loaded on the page (e.g., https://r.wdfl.co/rw.js). Implement a Consent Management Platform (CMP) check so that any third-party tracking script is only appended to the DOM after the user provides explicit consent (e.g., 'Allow analytics' toggle). Refactor the code to conditionally load the script, or replace with a privacy-friendly alternative. Add a Content-Security-Policy header restricting script-src to 'self' and trusted domains, and ensure IP anonymization or minimal data collection for any unavoidable third-party analytics. Example: if (userConsented('tracking')) { loadScript('https://r.wdfl.co/rw.js'); } else { do not load; show privacy banner; }
Why it's a bug
The network activity shows a request to a third-party domain (https://r.wdfl.co/rw.js) that appears to be a tracking script. Without clear evidence of a user consent prompt or CMP gating, this script could collect user identifiers (IP, device info, behavior) and enable cross-site tracking, which may violate privacy expectations and regulatory requirements.
Why it might not be a bug
If a consent management platform (CMP) is present and properly gating third-party scripts, this would be expected behavior. The logs do not reveal UI state or consent decisions, so the issue cannot be definitively deemed a bug without confirming the presence and operation of consent controls.
Suggested Fix
Gate all third-party tracking scripts behind explicit user consent. Integrate a CMP to obtain consent before loading https://r.wdfl.co/rw.js. Defer or conditionally load the script only after consent is given. Consider alternatives that minimize data sharing (privacy-preserving analytics). Implement a strict Content-Security-Policy to limit third-party script loading and anonymize collected data where possible.
Why Fix
Ensuring consent-gated loading of tracking scripts protects user privacy, aligns with data protection regulations, reduces cross-site tracking risk, and preserves user trust.
Route To
Frontend Engineer / Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
https://r.wdfl.co/rw.js2
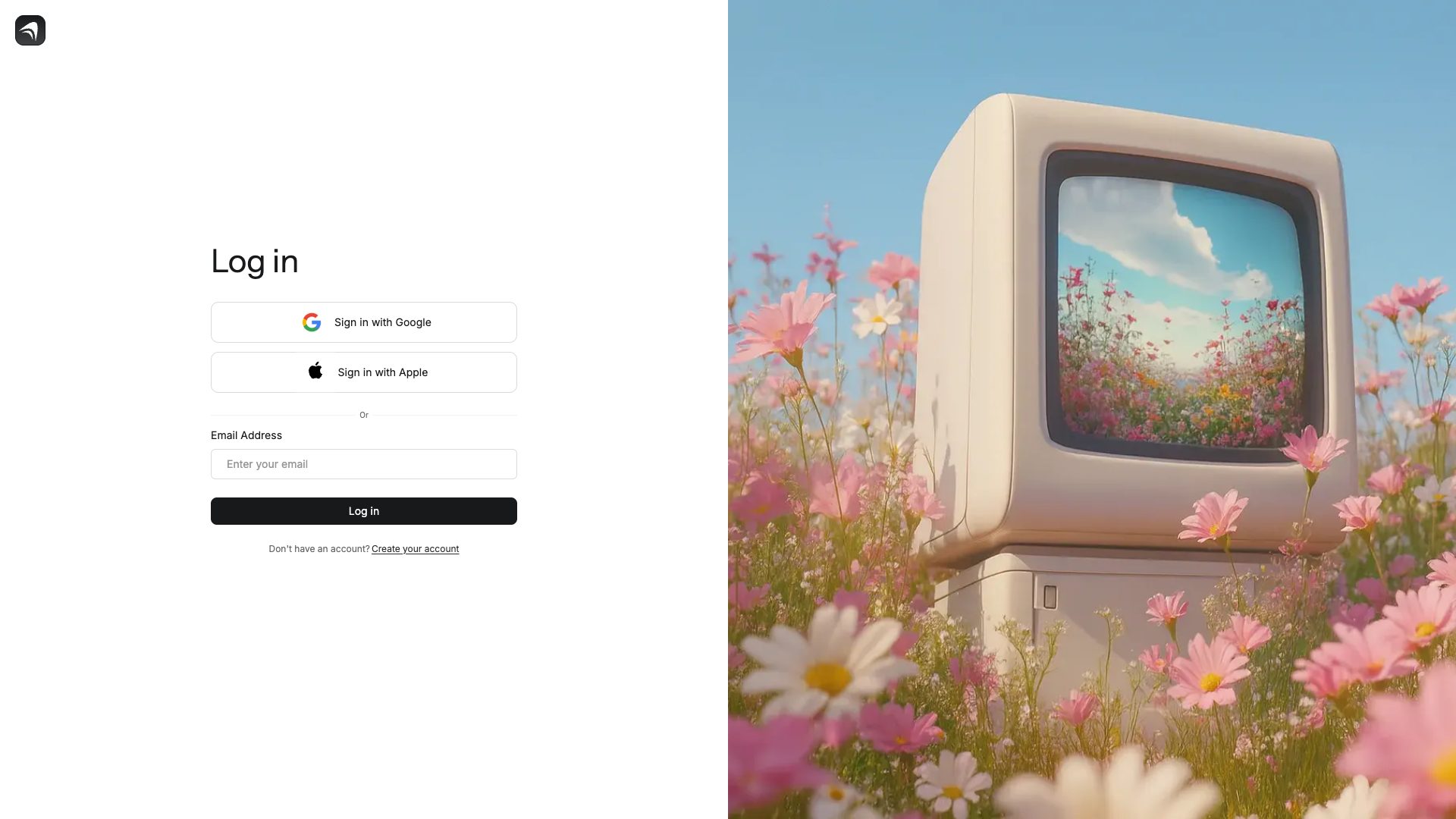
CORS misconfiguration causing cross-origin login request blocked
CRIT P9
Prompt to Fix
Problem: The login cross-origin request is blocked due to missing CORS headers on the login endpoint. Remediation: On the backend API (login endpoint), configure CORS to allow legitimate origin(s) used by the frontend. Steps:\n1) Determine trusted origins (e.g., https://www.create.xyz, https://www.createanything.com).\n2) In server config or middleware, set Access-Control-Allow-Origin to a specific origin or a dynamic allowed-origin list, not '*' if credentials are involved.\n3) If credentials are required, set Access-Control-Allow-Credentials: true and ensure cookies or tokens are transmitted securely (HttpOnly, Secure, SameSite).\n4) Ensure Access-Control-Allow-Methods includes POST, GET, OPTIONS as needed; Access-Control-Allow-Headers include Content-Type, Authorization, and any custom headers.\n5) Add Vary: Origin to responses so caches differentiate by origin.\n6) Validate with a preflight OPTIONS request and a test login flow from the frontend origins.\n7) Review any proxy or gateway that could strip these headers and fix at the edge if needed.
Why it's a bug
The browser is blocking a cross-origin login request due to the absence of the Access-Control-Allow-Origin header on the response. This indicates the backend does not properly permit cross-origin requests (or credentials) for the login flow, which can break legitimate user sessions and suggests potential broader misconfigurations that could impact security controls. In production, such misconfigurations can lead to login failures, user frustration, and potential data exposure risk if exploited in certain configurations.
Why it might not be a bug
If the login endpoint is strictly same-origin and cross-origin requests are not expected, this behavior could be expected. However, the log shows an actual cross-origin attempt, indicating a misconfiguration rather than a benign constraint. This should be investigated and corrected to ensure legitimate flows work and to minimize potential attack surface.
Suggested Fix
Configure CORS properly on the login endpoints. Do not use wildcard origins when credentials are involved. Specify the exact trusted origin(s) in Access-Control-Allow-Origin, enable Access-Control-Allow-Credentials as needed, and include Access-Control-Allow-Methods and Access-Control-Allow-Headers as appropriate. Add Vary: Origin header. Verify preflight requests succeed and that credentials (if used) are transmitted securely (HttpOnly, Secure, SameSite).
Why Fix
Correct CORS configuration prevents cross-origin request failures that disrupt login flows and reduces potential exposure from misconfigured responses. It also improves security posture by ensuring only trusted origins can interact with sensitive authentication endpoints.
Route To
Backend API Engineer
Page
Tester
Sharon · Security Console Log Analyzer
Technical Evidence
Console:
[ERROR] Access to fetch at 'https://www.createanything.com/login?_rsc=aoevz' (redirected from 'https://www.create.xyz/login?_rsc=aoevz') from origin 'https://www.create.xyz' has been blocked by CORS policy: Response to preflight request doesn't pass access control check: No 'Access-Control-Allow-Origin' header is present on the requested resource.Network:
https://www.create.xyz/login?_rsc=aoevz; https://www.createanything.com/login?_rsc=aoevz3
CORS preflight failure blocking login requests between create.xyz and createanything.com
CRIT P10
Prompt to Fix
Problem: CORS preflight blocked for login API at https://www.createxyz/login?_rsc=aoevz; origin https://www.create.xyz. Action: 1) Confirm the login service domain and ensure CORS headers are set on responses (Access-Control-Allow-Origin with the requesting origin or a permissive wildcard as appropriate). 2) Ensure OPTIONS preflight responses include Access-Control-Allow-Methods and Access-Control-Allow-Headers. 3) Verify API gateway/proxy does not strip CORS headers. 4) If microservices are involved, propagate CORS settings across services. 5) Deploy fix and validate by performing a cross-origin login flow.
Why it's a bug
Login authentication is blocked due to missing CORS headers, preventing users from signing in and completing tasks; this is a critical user flow.
Why it might not be a bug
Cross-origin calls can be legitimate, but the server must explicitly allow the origin. Absence of Access-Control-Allow-Origin indicates misconfiguration rather than a feature.
Suggested Fix
Configure the login API to return proper CORS headers (Access-Control-Allow-Origin: https://www.create.xyz or * as appropriate), allow necessary methods (OPTIONS, POST, GET), and allowed headers. Ensure OPTIONS preflight requests are handled correctly and that API gateway/proxy does not strip CORS headers. Validate downstream services to consistently apply CORS policy.
Why Fix
Restores the login flow, preventing user friction and ensuring authentication works across domains.
Route To
Backend Engineer / API Security Engineer
Page
Tester
Sharon · Security Tester
Technical Evidence
Console:
Access to fetch at 'https://www.createanything.com/login?_rsc=aoevz' (redirected from 'https://www.create.xyz/login?_rsc=aoevz') from origin 'https://www.create.xyz' has been blocked by CORS policy: Response to preflight request doesn't pass access control check: No 'Access-Control-Allow-Origin' header is present on the requested resource.Network:
https://www.createanything.com/login?_rsc=aoevz (preflight blocked by CORS)