A-90%
Quality Score
4
Pages
44
Issues
8.1
Avg Confidence
7.8
Avg Priority
19 Critical15 High10 Medium

>_ Testers.AI
AI Analysis
Dev.Prosusagents was tested and 44 issues were detected across the site. The most critical finding was: Exposure of development/staging endpoints in production network traffic. Issues span Security, A11y, Performance, Other categories. Persona feedback rated Visual highest (9/10) and Accessibility lowest (6/10).
Qualitative Quality
Dev.Prosusagents
Category Avg
Best in Category
Pages Tested · 4 screenshots
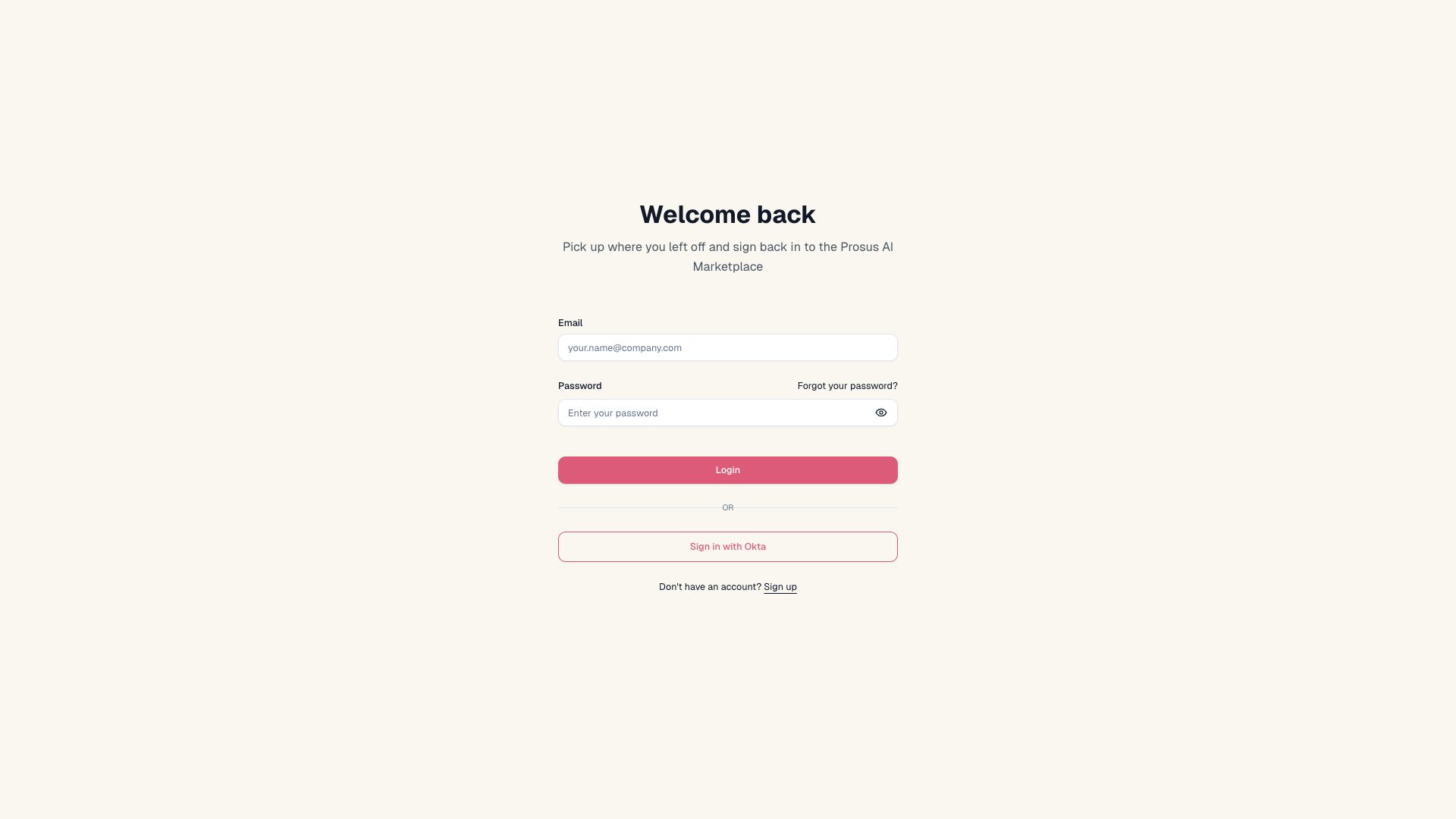
Homepage
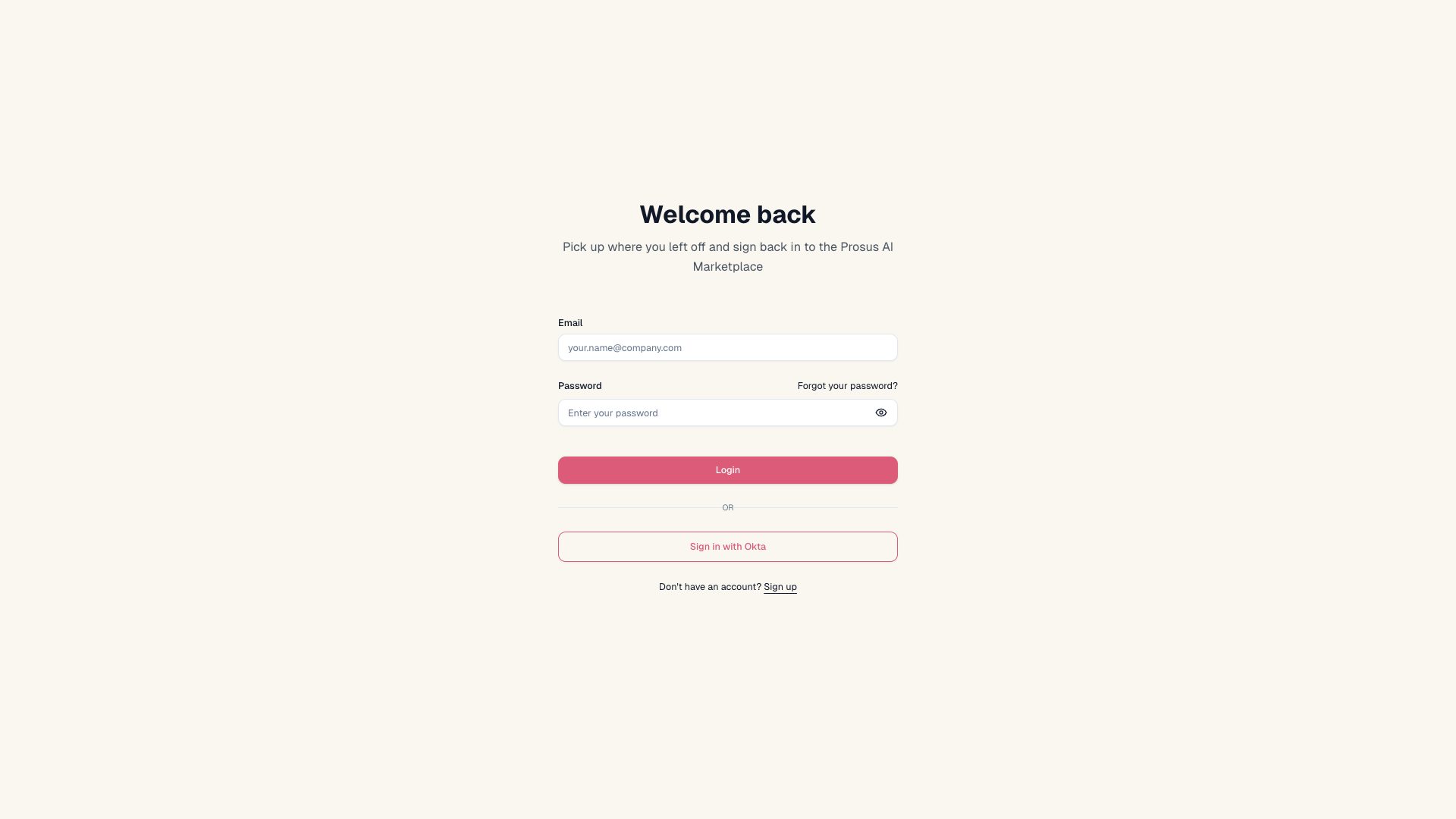
dev.prosusagents.com.auth.dashboard
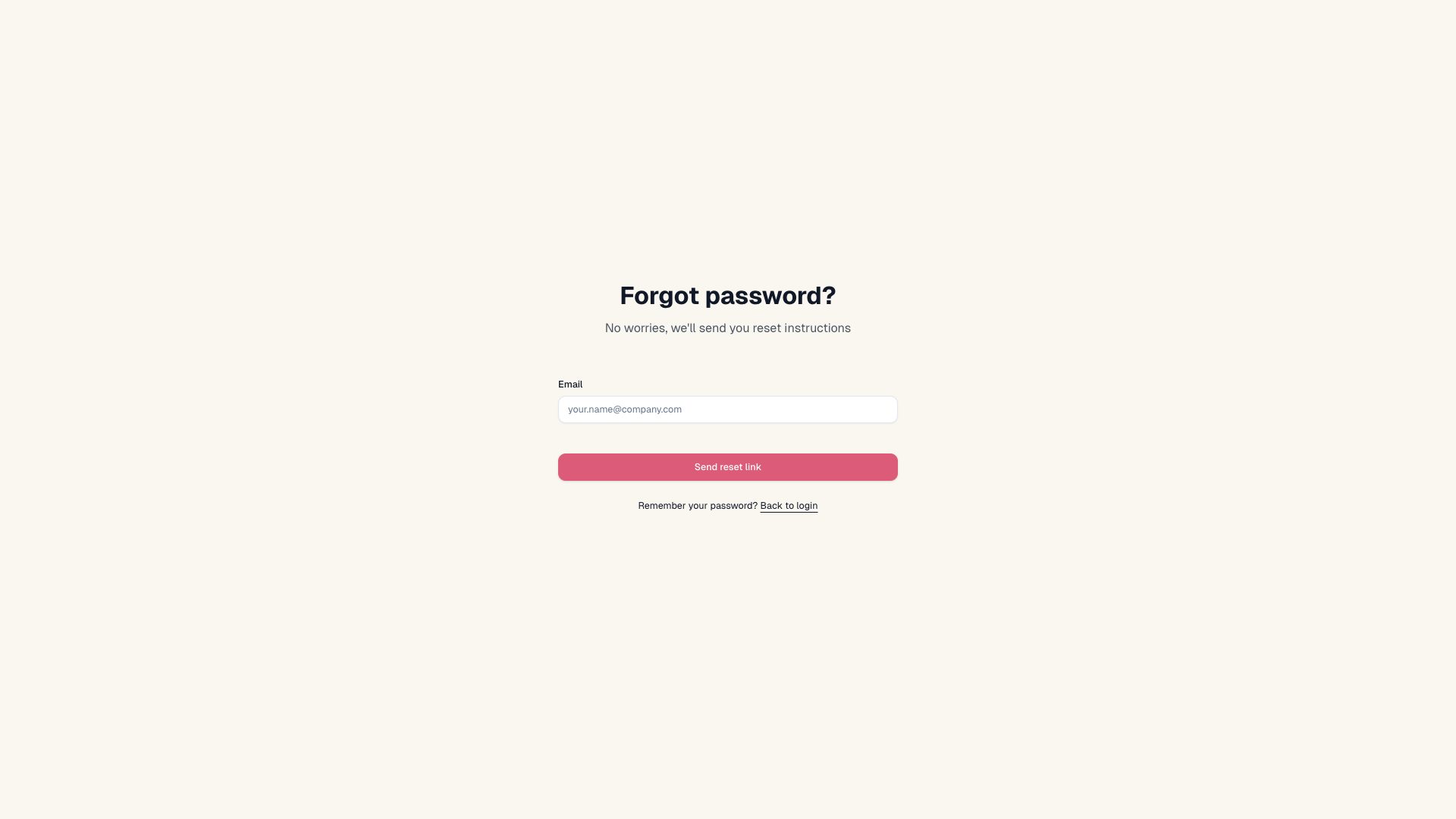
dev.prosusagents.com.auth.dashboard
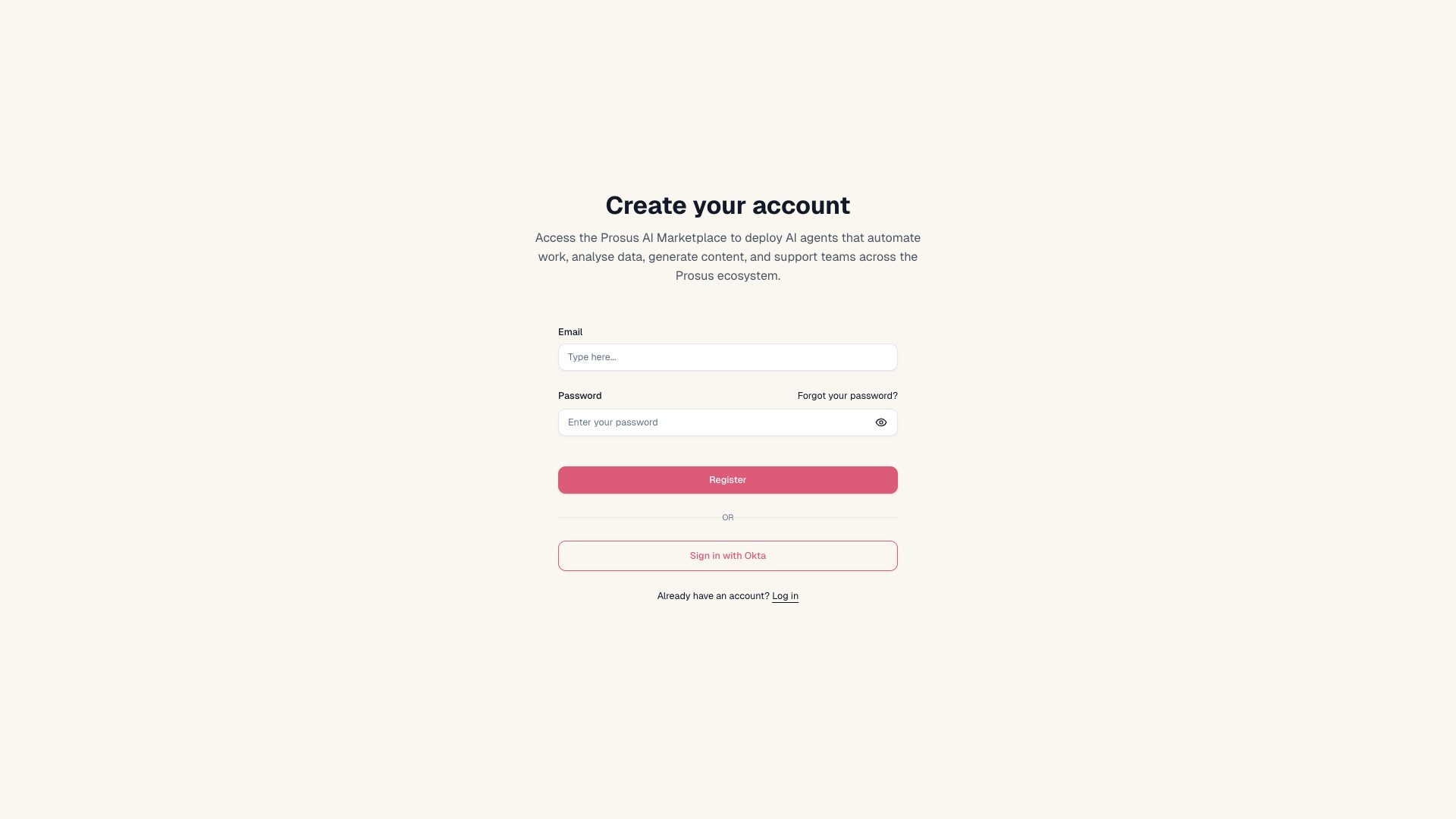
dev.prosusagents.com.auth.dashboard
Detected Issues · 44 total
1
Exposure of development/staging endpoints in production network traffic
CRIT P9
Prompt to Fix
Prompt for AI coder: Update the production build to stop referencing dev endpoints. Locate environment config files and replace any base API URL pointing to dev.api.prosusagents.com or dev.prosusagents.com with the production base URL api.prosusagents.com (or equivalent production domain). Ensure frontend code uses a single, environment-controlled API_BASE_URL that is set via build-time environment variables. Remove dev DNS records or restrict access to dev endpoints (VPN/allowlist). Add a CI check to fail builds if any dev.* endpoints are present in the production build assets or config.
Why it's a bug
The traffic includes requests to dev subdomains (e.g., dev.prosusagents.com, dev.api.prosusagents.com). This indicates staging/development endpoints are reachable from production-like environments. Exposure of non-production endpoints can reveal weaker security controls, misconfigurations, or internal services to end users or malicious actors, increasing risk of data exposure or targeted attacks.
Why it might not be a bug
If this is strictly a controlled testing environment with restricted access, it could be intentional. However, public or semi-public usage showing dev endpoints in production-like traffic strongly suggests a misconfiguration that should be resolved to prevent exposure and maintain proper environment separation.
Suggested Fix
Replace all dev endpoints with production endpoints in the frontend and API configuration for production builds. Use environment-based configuration (e.g., REACT_APP_API_BASE_URL) that points to api.prosusagents.com in production. Remove or firewall dev.* DNS records from public exposure, or put dev endpoints behind VPN/IP allowlists. Implement CI checks to prevent pushing dev URLs into production builds.
Why Fix
Fixing this reduces attack surface by preventing access to staging infrastructure, ensures consistent security controls across environments, and lowers risk of data leakage or exploitation stemming from misconfigured endpoints.
Route To
Security Engineer
Page
Tester
Sharon · Security Networking Analyzer
Technical Evidence
Network:
GET https://dev.api.prosusagents.com/api/user/profile2
Hardcoded dev API endpoint URLs in client code
HIGH P8
Prompt to Fix
Refactor the API call logic to read base URL from environment config (e.g., import.meta.env.VITE_API_BASE_URL). Use a centralized API client to construct endpoints, and ensure the production build uses the correct base URL. Remove hardcoded dev URLs from frontend code.
Why it's a bug
The application calls dev-specific endpoints (https://dev.prosusagents.com/register) directly from the frontend. This hardcoding can lead to environment drift, accidental exposure of dev domains, and breaks in production.
Why it might not be a bug
In some teams, dev endpoints are temporarily used for testing; however, hardcoding them without a config layer is generally risky and not production-friendly.
Suggested Fix
Replace hardcoded URLs with a centralized API client configured via environment variables (e.g., VITE_API_BASE_URL) and use a single base URL with endpoint paths. Add proper fallback and error handling. Remove any dev-only URLs from production builds.
Why Fix
Promotes proper environment-based configuration, reduces security/ops risk, and improves maintainability and testability across environments.
Route To
Frontend/Platform Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Network:
GET https://dev.prosusagents.com/register - Status: 2003
Repeated 401 Unauthorized errors on resource loads
CRIT P9
Prompt to Fix
Identify all frontend API calls that emit a 401 Unauthorized on resource load. For each call: (1) ensure Authorization: Bearer <token> is attached; (2) implement a global token refresh on 401, then retry the original request once; (3) if refresh fails, redirect to login with a clear message; (4) centralize API client to manage tokens and error handling; (5) add user-facing error messaging instead of silent console errors; (6) reduce console noise by deduplicating 401 logs and including endpoint context.
Why it's a bug
Two resource load failures returning 401 Unauthorized indicate authentication is failing for protected endpoints. This prevents data from loading and blocks user tasks. The errors are surfaced in console but may not be properly surfaced in the UI, suggesting gaps in auth handling and token lifecycle management.
Why it might not be a bug
If the user is legitimately unauthenticated, 401 on protected resources can be expected. However, the presence of multiple 401s across resources suggests a broken or incomplete authentication flow and a poor UX unless explicitly handled by login prompts.
Suggested Fix
1) Audit all API calls for proper Authorization headers and valid tokens. 2) Implement a robust token refresh flow: on 401, attempt token refresh; if successful, retry the original request once. 3) If refresh fails, force a user-friendly login prompt and halt further protected requests until authentication is restored. 4) Centralize API client logic to prevent duplicate requests and to normalize 401 handling across endpoints. 5) Add telemetry to capture endpoint, status, and auth state on 401; debounce noisy logs and surface user-facing errors instead of silent console logs.
Why Fix
Fixing the authentication flow ensures protected data loads correctly, enables task completion, and reduces silent failures and console noise that confuse users and developers.
Route To
Frontend Engineer
Page
Tester
Sharon · Security Tester
Technical Evidence
Console:
[ERROR] Failed to load resource: the server responded with a status of 401 ()Network:
Unknown resource URLs; likely protected API endpoints returning 401 due to missing/expired auth tokens