B-82%
Quality Score
7
Pages
113
Issues
8.0
Avg Confidence
7.9
Avg Priority
49 Critical47 High17 Medium

>_ Testers.AI
AI Analysis
Home.Pulsesms.App was tested and 113 issues were detected across the site. The most critical finding was: Unconsented third-party analytics tracking (Google Tag Manager). Issues span Security, Legal, Performance, A11y categories. Persona feedback rated Visual highest (7/10) and Accessibility lowest (6/10).
Qualitative Quality
Home.Pulsesms.App
Category Avg
Best in Category
Pages Tested · 7 screenshots
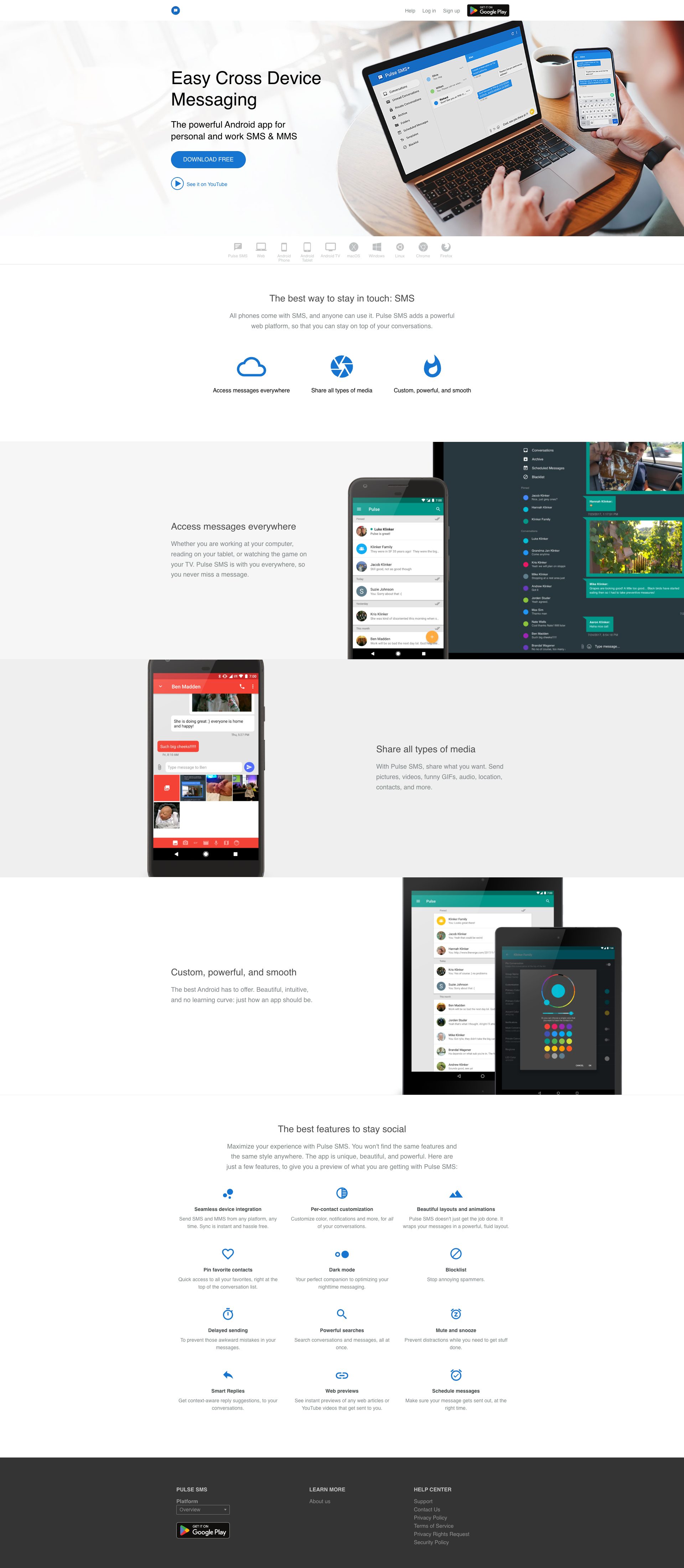
Homepage

home.pulsesms.app.overview

home.pulsesms.app.overview
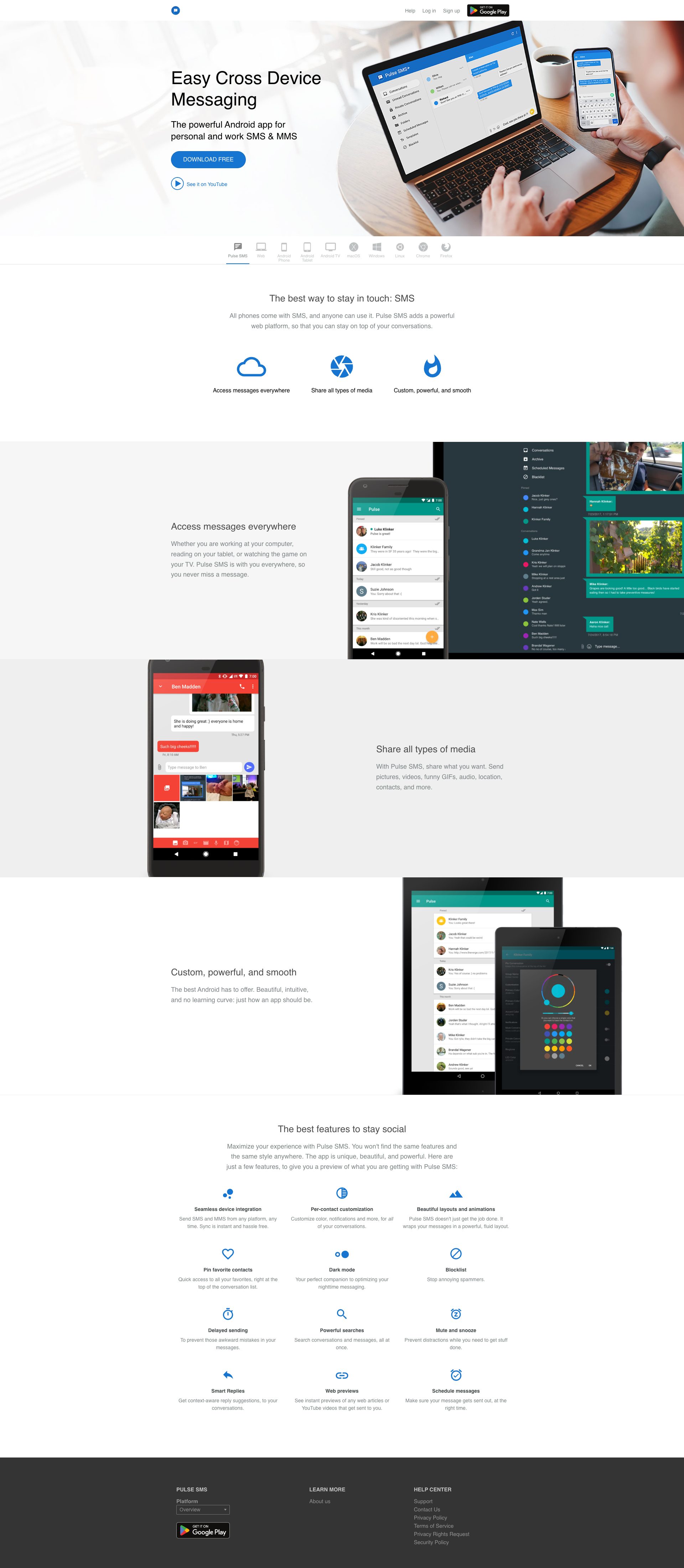
home.pulsesms.app.overview

home.pulsesms.app.overview
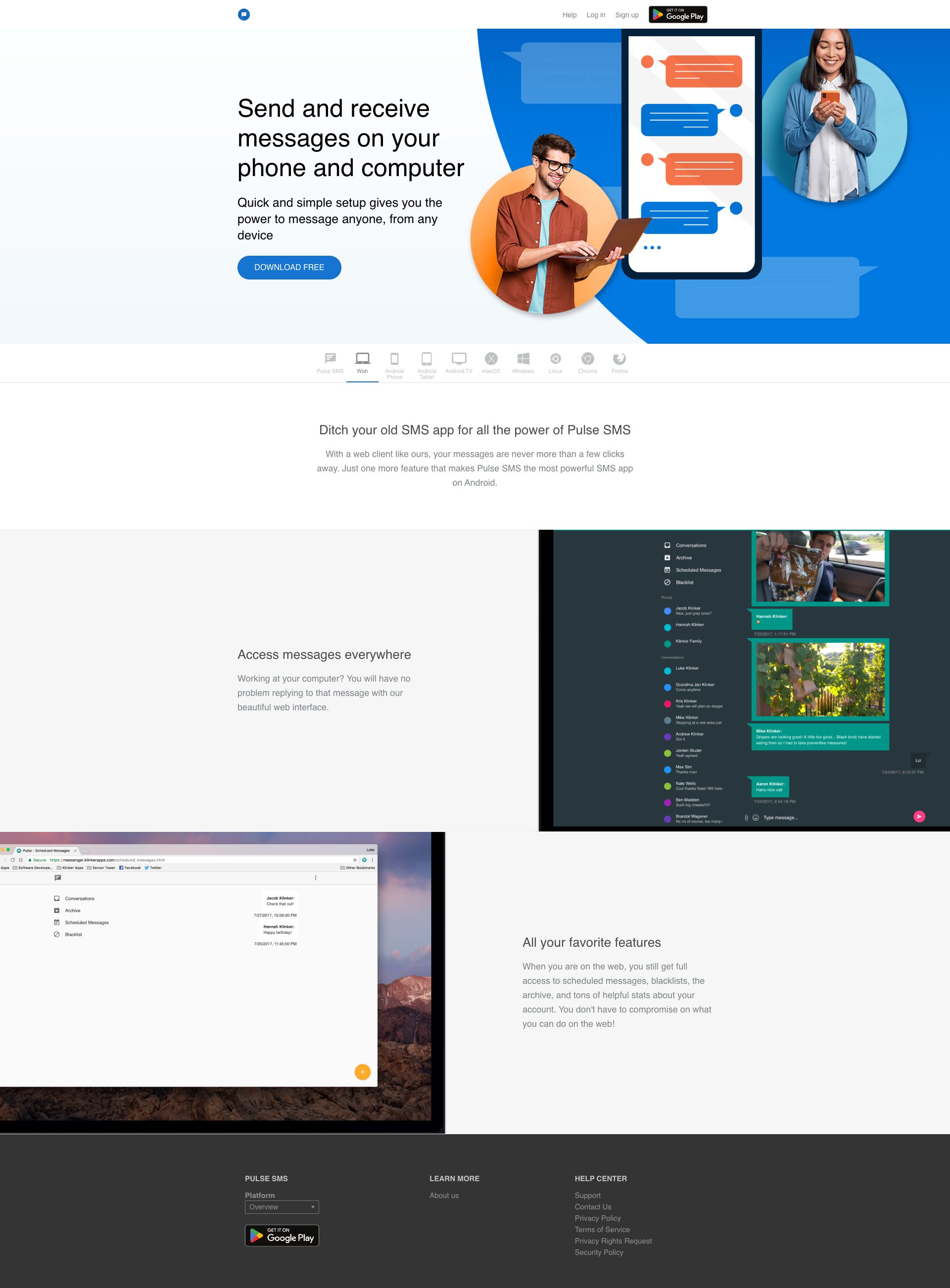
home.pulsesms.app.overview

home.pulsesms.app.overview
Detected Issues · 113 total
1
Unconsented third-party analytics tracking (Google Tag Manager)
CRIT P9
Prompt to Fix
Add a consent banner for analytics. Modify the app so that the GTM script and GA libraries are only loaded after user consents to tracking. Include an option to opt-out, enable IP anonymization in GA, and ensure analytics data is minimized and not sent until consent is granted.
Why it's a bug
The page loads Google Tag Manager (GTM) script (GT M-5VVJ3QJH) and related analytics resources without a visible explicit consent mechanism. This enables third-party data collection and potential cross-site tracking without user opt-in, which is a privacy risk and could violate privacy regulations or user expectations.
Why it might not be a bug
If a comprehensive consent flow is implemented elsewhere (e.g., in a privacy policy or hidden behind consent), this might be acceptable. The logs do not show any consent gating, so this remains a risk.
Suggested Fix
Implement a visible, user-consent-driven mechanism before loading GTM/GA scripts. Load analytics only after explicit opt-in, enable IP anonymization, provide an easy opt-out, and consider deferring analytics until after user interaction. Consider loading GTM as a first-party script with strict data minimization.
Why Fix
Protect user privacy, reduce third-party data sharing, and improve user trust and regulatory compliance (e.g., GDPR/CCPA).
Route To
Privacy Engineer / Frontend Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
GET https://www.googletagmanager.com/gtm.js?id=GTM-5VVJ3QJH2
AI/LLM endpoints loaded on page load without user consent
CRIT P9
Prompt to Fix
Implement a user consent flow before initiating any AI/ML endpoint calls detected on page load. Add a consent banner that explains data shared with AI services, provide a reject/allow option, and gate all AI-related network requests behind this consent. Refactor initialization to defer AI script loading until after consent is given.
Why it's a bug
Console output shows explicit detection of AI endpoints ('⚠️ AI/LLM ENDPOINT DETECTED') and network requests to AI-related domains (e.g., mastodon.maplemedia.tech/mastodon_2.js, geolocation.json). Loading AI/LLM endpoints on initial page load can trigger unexpected data sharing and privacy concerns without user consent or clear disclosure.
Why it might not be a bug
If those AI endpoints are essential for core functionality and already governed by a consent flow, this may be intentional. However, the logs strongly suggest endpoints are active without visible consent UX, making it a high-risk area.
Suggested Fix
Move AI/LLM endpoint calls behind an explicit user consent flow (cookie/privacy banner). Implement lazy-loading or feature-flag gating for any AI integrations. Ensure privacy disclosures and controls are presented before initiating data-heavy or model-invoking requests.
Why Fix
Protects user privacy, reduces potential compliance risk, and aligns with best practices for GenAI/AI integrations by requiring consent before data is sent to AI services.
Route To
Frontend Engineer / Privacy Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
⚠️ AI/LLM ENDPOINT DETECTEDNetwork:
https://mastodon.maplemedia.tech/mastodon_2.js; https://mastodon.maplemedia.tech/geolocation.json3
Geolocation data exposed in console logs (privacy risk)
CRIT P9
Prompt to Fix
Audit all console.log / logging statements that handle geolocation data in the Mastodon frontend. Replace direct prints of geolocation data with redacted indicators (e.g., 'geo data redacted' or 'geo detected (redacted)'). Remove prints of JSHandle@object or actual coordinate values. Add a helper logger that rejects any geolocation data from logs. Ensure geolocation data is never sent to console, logs, or telemetry in production builds. After changes, run privacy-focused log checks to confirm no geolocation data appears in console logs.
Why it's a bug
Logs indicate geolocation data is captured and logged (references to geolocation data handles and GeolocationRuleType.isApplicable). Exposing geolocation information in console logs can be accessed by developers, extensions, or potential attackers, constituting sensitive PII and violating privacy best practices and likely regulatory expectations.
Why it might not be a bug
If geolocation data is strictly redacted or never actually logged (only internal handles are shown), this might be lower risk. However, explicit log lines mention geolocation data objects, which implies potential exposure rather than a fully sanitized approach.
Suggested Fix
Remove or redact all geolocation data from console logs. Implement a sanitized logging approach that never prints actual geolocation values or object handles. Example: replace geolocation log statements with generic indicators (e.g., 'geo data detected (redacted)') and ensure any geolocation retrieval is performed server-side or with strict access controls. Audit all code paths that log location data and implement a logging guard to prevent sensitive data from being emitted in any console or telemetry.
Why Fix
Protecting user location data is critical to privacy and security. Preventing exposure of geolocation in logs reduces risk of data leakage, abuse, and regulatory non-compliance, and preserves user trust.
Route To
Frontend Engineer / Privacy Engineer
Page
Tester
Pete · Privacy Console Log Analyzer
Technical Evidence
Console:
GeolocationRuleType.isApplicable true JSHandle@object JSHandle@object GeolocationRuleType.isApplicable false JSHandle@object JSHandle@object got geo data JSHandle@object