B83%
Quality Score
7
Pages
109
Issues
8.2
Avg Confidence
8.0
Avg Priority
48 Critical46 High15 Medium

>_ Testers.AI
AI Analysis
Homspector was tested and 109 issues were detected across the site. The most critical finding was: AI/LLM endpoints detected invoked on page load (potential GenAI leakage and performance risk). Issues span Security, A11y, Performance, Other categories. Persona feedback rated Visual highest (8/10) and Accessibility lowest (5/10).
Qualitative Quality
Homspector
Category Avg
Best in Category
Pages Tested · 7 screenshots

Homepage
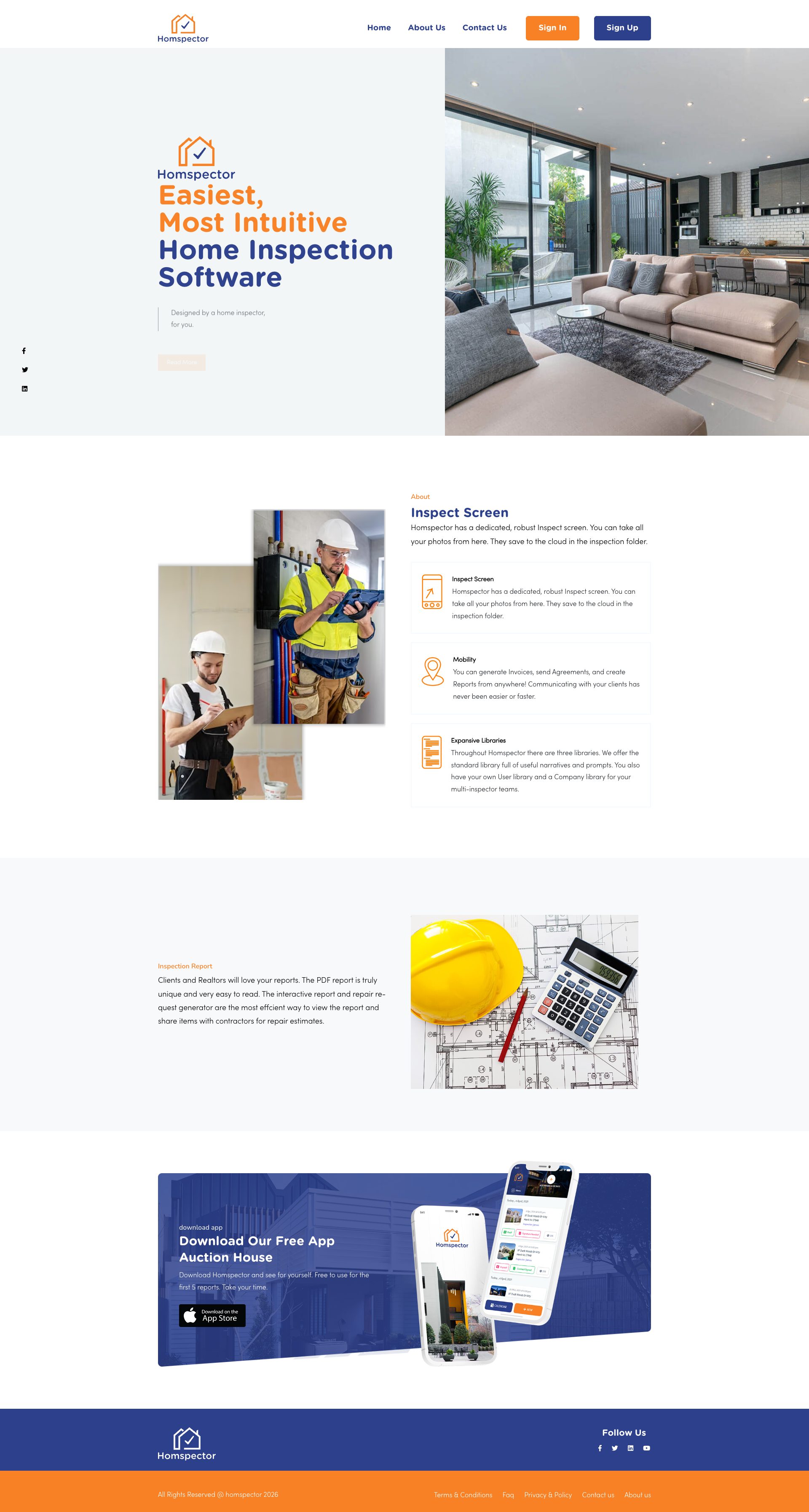
homspector.com.web.

homspector.com.web.
homspector.com.web.
homspector.com.web.

homspector.com.web.
homspector.com.web.
Detected Issues · 109 total
1
AI/LLM endpoints detected invoked on page load (potential GenAI leakage and performance risk)
CRIT P10
Prompt to Fix
Refactor the page so that no LLM/AI endpoint calls are executed on initial paint. Introduce a consent check and a feature flag to enable AI usage. Implement lazy-loading for AI resources with a robust backoff strategy and remove any internal AI endpoint exposure in production builds.
Why it's a bug
Logs show '⚠️ AI/LLM ENDPOINT DETECTED' during page activity, implying AI service calls on initial load. This can cause performance degradation, data exposure without consent, and hidden prompts being sent without user awareness.
Why it might not be a bug
If the product deliberately uses on-load AI calls for personalization, it should be clearly disclosed, gated behind user consent, and implemented with lazy loading and proper privacy safeguards.
Suggested Fix
Delay or gate all LLM/AI calls until explicit user action or consent. Move AI calls behind feature flags, implement lazy loading with exponential backoff, log clearly when AI is used, and remove any debug/endpoint-detection markers from production code.
Why Fix
Reduces performance impact, protects user privacy, and aligns with best practices for AI integrations.
Route To
Frontend Architect / Security & Privacy Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
⚠️ AI/LLM ENDPOINT DETECTED2
Unconsented third-party font loading enabling cross-site tracking
CRIT P9
Prompt to Fix
Actionable fix: 1) Download and host the used font families (Poppins, Nunito Sans) locally (WOFF2/WOFF). 2) Update HTML/CSS to reference locally hosted fonts via @font-face declarations. 3) Implement a user consent mechanism before loading any non-essential third-party fonts. 4) Add a Content-Security-Policy header restricting font-src to 'self'. 5) Validate that fonts load after consent without triggering requests to fonts.googleapis.com or fonts.gstatic.com.
Why it's a bug
The page loads fonts from external third-party domains (fonts.googleapis.com, fonts.gstatic.com). This can trigger cross-site tracking and font-based fingerprinting without explicit user consent or clear disclosure, exposing user browser characteristics and visiting patterns.
Why it might not be a bug
Using external fonts is common and can be privacy-preserving if consent is obtained and disclosures are provided. Without explicit consent indicators in the request flow, this remains a privacy risk.
Suggested Fix
Host fonts locally (self-host) or load fonts only after user consent. Implement a consent banner for all non-essential third-party resources, and enforce a strict Content-Security-Policy restricting font sources to self. Replace external font links with locally hosted equivalents and verify fonts load correctly after consent.
Why Fix
Eliminates passive data leakage and fingerprinting opportunities from third-party font requests, improving user privacy and aligning with privacy-by-design principles.
Route To
Frontend Security/Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Console:
GET https://fonts.googleapis.com/css?family=Poppins:300,400,500,600,700|Varela+Round - Status: 200Network:
https://fonts.googleapis.com/css?family=Poppins:300,400,500,600,700|Varela+Round; https://fonts.gstatic.com/s/nunitosans/v19/pe0TMImSLYBIv1o4X1M8ce2xCx3yop4tQpF_MeTm0lfGWVpNn64CL7U8upHZIbMV51Q42ptCp7t1R-s.woff23
Device fingerprinting library loaded from CDN (FingerprintJS) enables browser/device fingerprinting
CRIT P9
Prompt to Fix
Remove or defer loading FingerprintJS (fp.min.js) from CDN, or wrap in a consent-guarded module. Add a privacy-consent banner for any device/browser fingerprinting usage, and implement an opt-out. If fingerprinting is necessary for security/anti-abuse, implement server-side checks or privacy-preserving fingerprinting and only collect minimal, non-identifying data. Update privacy policy and disclosures accordingly.
Why it's a bug
Loading a fingerprinting library collects browser/OS characteristics to generate a unique device fingerprint used for cross-site tracking and user profiling. The client loads this script from a third-party CDN without evident consent flow, creating significant privacy risk.
Why it might not be a bug
Potential legitimate use for security/anti-abuse; if explicit user consent is obtained and documented, the risk is mitigated. In the observed activity, there is no visible consent flow.
Suggested Fix
Remove the fingerprinting script or gate its usage behind explicit user consent. If fingerprinting is required for security, implement a consent banner, provide an opt-out, and consider server-side checks or privacy-preserving alternatives. Consider hosting locally only after consent and enforce a strict CSP to restrict third-party fingerprinting.
Why Fix
Reduces risk of cross-site tracking and regulatory exposure, improves user trust and privacy compliance.
Route To
Frontend Engineer / Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
GET https://cdn.jsdelivr.net/npm/@fingerprintjs/fingerprintjs@4/dist/fp.min.js - Status: 200