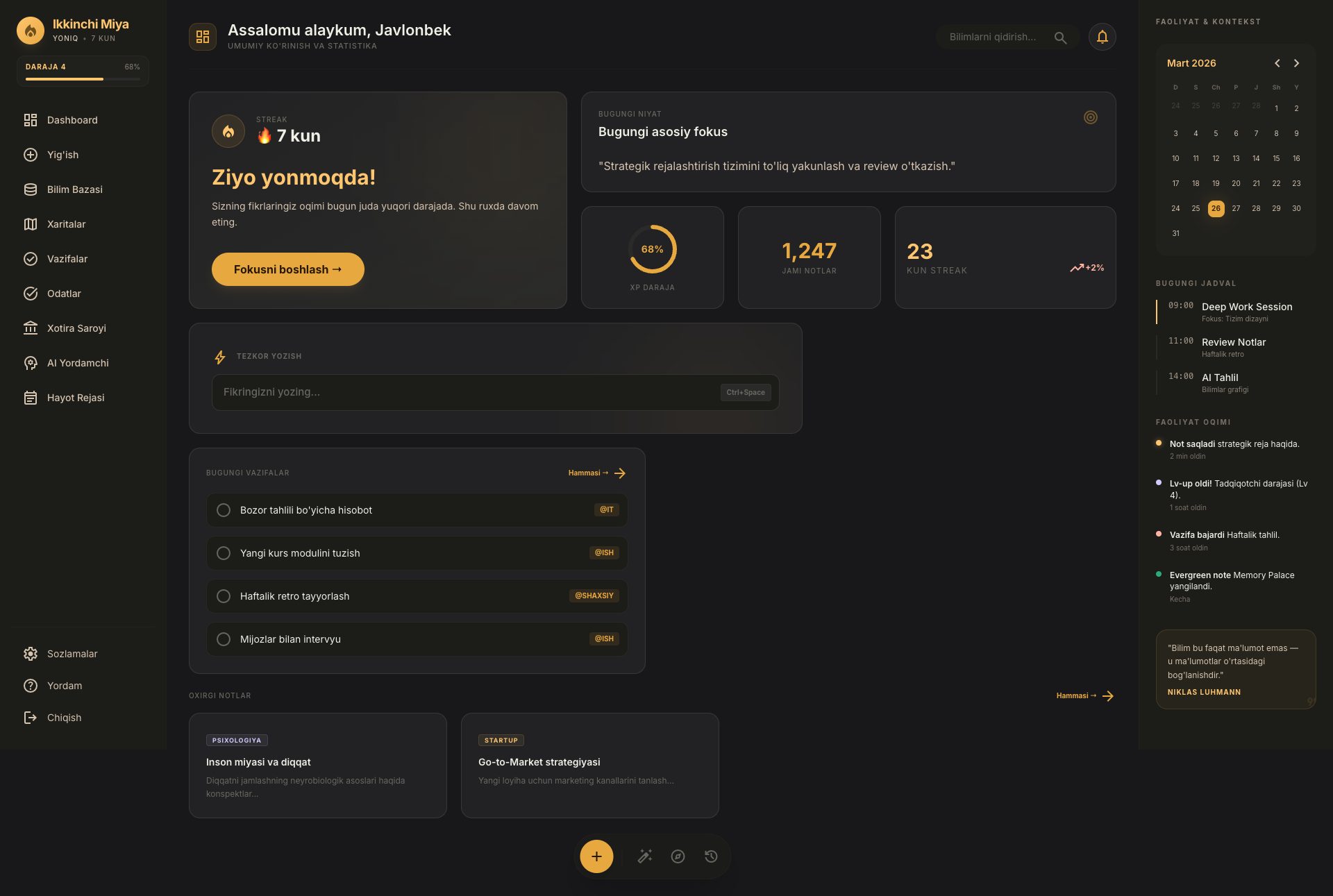
B+87%
Quality Score
7
Pages
78
Issues
7.9
Avg Confidence
7.7
Avg Priority
32 Critical30 High15 Medium1 Low

>_ Testers.AI
AI Analysis
Ikkinchi-Miya.Vercel.App was tested and 78 issues were detected across the site. The most critical finding was: Third-Party Data Sharing via Google Font Resources. Issues span A11y, Performance, Other, UX categories. Persona feedback rated Visual highest (8/10) and Accessibility lowest (6/10).
Qualitative Quality
Ikkinchi-Miya.Vercel.App
Category Avg
Best in Category
Pages Tested · 7 screenshots
Homepage

ikkinchi
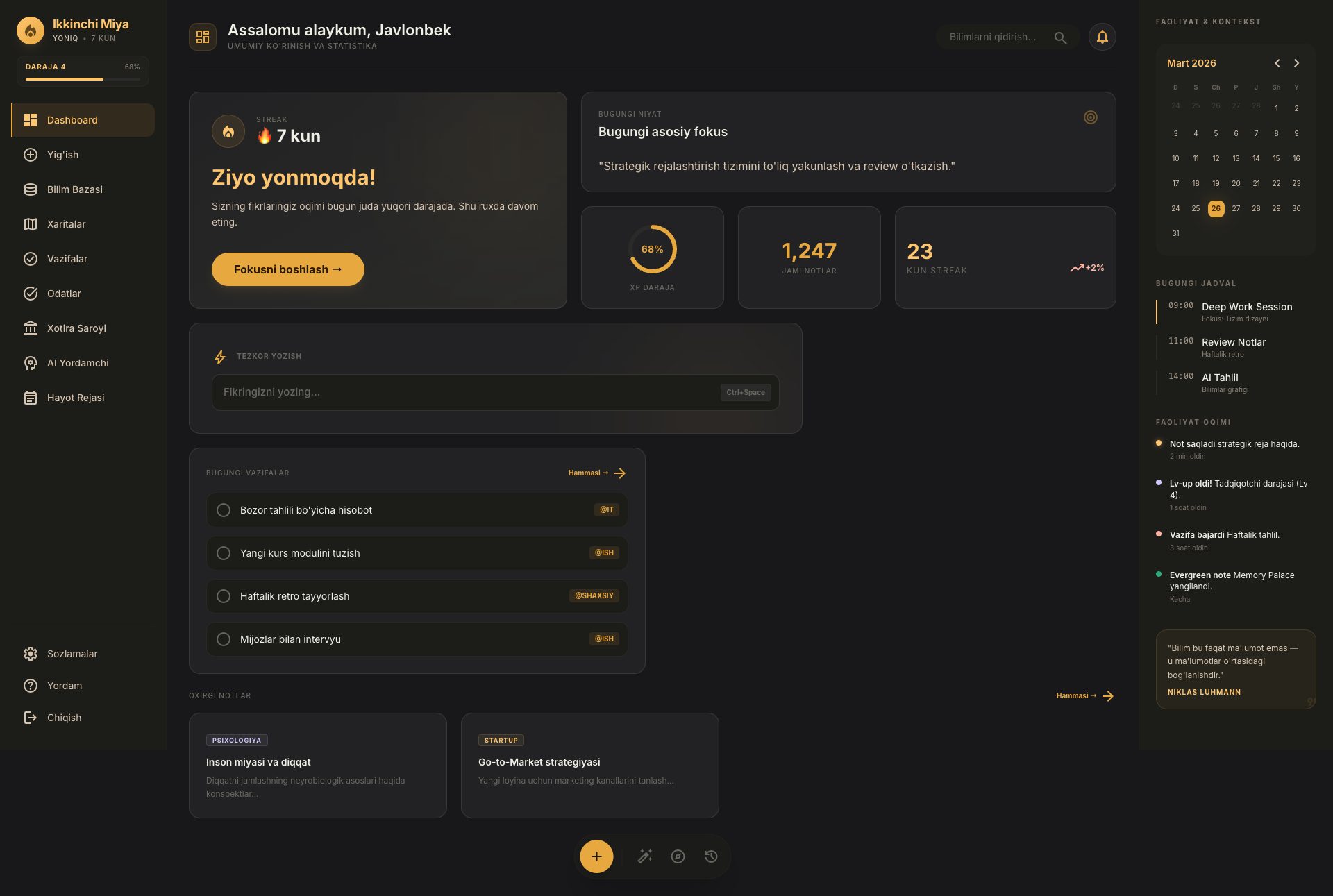
ikkinchi

ikkinchi

ikkinchi

ikkinchi
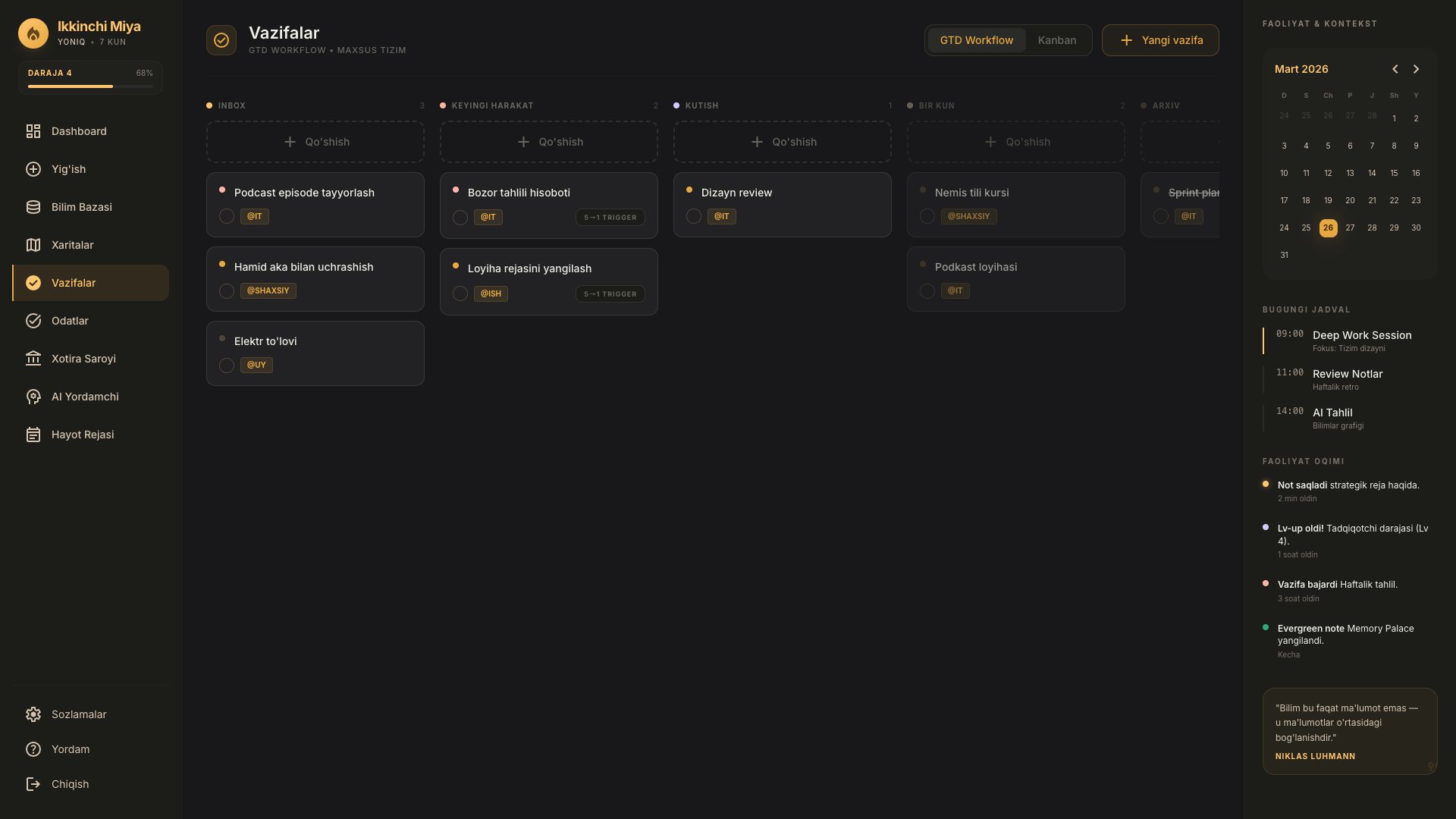
ikkinchi
Detected Issues · 78 total
1
Third-Party Data Sharing via Google Font Resources
CRIT P9
Prompt to Fix
Actionable fix: Replace remote font loading with locally hosted fonts. 1) Download and host the Inter, Newsreader, and Material Symbols font files on the app’s own domain (e.g., /static/fonts/). 2) Update CSS references to point to /static/fonts/Inter-*.woff2, /static/fonts/Newsreader-*.woff2, etc. 3) Remove any fonts.googleapis.com and fonts.gstatic.com requests from the page. 4) If external fonts must remain, implement a user consent step before loading them and add a clear privacy notice describing data sharing with Google Fonts (IP, user agent, etc.). 5) Add a Content-Security-Policy header to restrict font-src to self (and trusted domains if external fonts are allowed after consent).
Why it's a bug
The page loads fonts from Google’s CDN (fonts.googleapis.com and fonts.gstatic.com). This causes the user’s IP address and device information to be transmitted to a 3rd party without any visible privacy disclosure or consent prompt. While common, it constitutes third-party data sharing and potential cross-site tracking, exposing user data to a provider the user did not explicitly authorize.
Why it might not be a bug
Fonts are standard assets and not user-generated content; many sites rely on CDNs for performance. Some teams may accept this as a normal trade-off and rely on existing privacy policies. However, without explicit consent or disclosure, it remains a privacy risk.
Suggested Fix
Host fonts locally (self-host) or use a permitted, opt-in font loading mechanism. Update CSS to reference locally served font files and remove dependency on fonts.googleapis.com and fonts.gstatic.com. If external fonts must remain, implement explicit consent for loading third-party fonts, and add a privacy notice describing data shared with the font provider. Consider a Content-Security-Policy with font-src self to block third-party font requests.
Why Fix
Eliminating or clearly controlling third-party font requests reduces exposure of IP addresses and device details to external providers, improves user privacy, and aligns with data minimization principles. It also reduces cross-site tracking risk and simplifies privacy compliance.
Route To
Frontend Engineer / Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
GET https://fonts.googleapis.com/css2?family=Inter:wght@300;400;500;600;700;800&family=Newsreader:ital,opsz,wght@0,6..72,300..800;1,6..72,300..800&display=swap - Status: N/A; GET https://fonts.gstatic.com/s/inter/v20/UcC73FwrK3iLTeHuS_nVMrMxCp50SjIa1ZL7.woff2 - Status: N/A2
AI/LLM endpoint calls trigger on page load (performance/data leakage risk)
CRIT P9
Prompt to Fix
In the client entry point, remove any AI/LLM endpoint calls that run on initial render. Move those calls behind a user action (e.g., click) or server-side precomputation. Wrap calls in try/catch, implement fallback UI, and ensure no sensitive data is sent without consent. Add a feature flag to enable/disable preloads and document the rationale.
Why it's a bug
Network activity shows AI/LLM endpoint usage detected during initial load ("⚠️ AI/LLM ENDPOINT DETECTED") and assets fetches. Auto-invoking LLMs on render can cause latency, unnecessary data transmission, and potential privacy concerns without user consent.
Why it might not be a bug
If pre-warming AI calls is a deliberate feature with user consent or a server-side optimization, it could be justified; however, there is no evidence of consent or justification in the screenshot/logs.
Suggested Fix
Defer LLM/embedding/API calls until explicit user action or move to a server-side preload with proper consent. Add feature flags and error handling; remove or isolate any debug AI-endpoint probes from production builds.
Why Fix
Improves performance, preserves user privacy, and aligns with expected UX by avoiding unexpected network activity.
Route To
Frontend Engineer / Full-Stack Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
⚠️ AI/LLM ENDPOINT DETECTEDNetwork:
GET https://ikkinchi-miya.vercel.app/assets/index-Dd8oKJ8Q.js - Status: 2003
Incomplete button definition in Page Content (truncated className)
CRIT P9
Prompt to Fix
Review the Page Content JSON for the buttons array. The last button entry ends with an incomplete className value ('round'). Replace with a valid Tailwind class (e.g., 'rounded-full') and ensure the entire JSON object is syntactically valid. Re-run the build and verify the UI renders all buttons correctly without errors.
Why it's a bug
The last button entry ends with an incomplete className value ('className":"px-4 py-1.5 round'), which will cause invalid JSON and likely broken rendering of that UI element. This is a direct artifact of AI-generated code and will fail in production.
Why it might not be a bug
If this is part of a draft/test scaffold, it might be intentional; however, in a real app, this would definitely break the UI rendering.
Suggested Fix
Complete the className value for the final button. For example: "className":"px-4 py-1.5 rounded-full text-xs font-bold tracking-widest uppercase whitespace-nowrap transition-all border border-[#F0EFE6]/10 text-[#68675F] hover:bg-[#222224] hover:text-[#F0EFE6] hover:border-[#E8A840]/20" and ensure the JSON object is properly closed.
Why Fix
Fixing this prevents a runtime UI rendering error and improves reliability and user experience. It also resolves a potential JSON parsing issue during build-time.
Route To
Frontend Engineer / React Developer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Network:
GET https://ikkinchi-miya.vercel.app/knowledge - Status: 200