B85%
Quality Score
4
Pages
50
Issues
7.8
Avg Confidence
7.8
Avg Priority
18 Critical23 High9 Medium

>_ Testers.AI
AI Analysis
Bedlam was tested and 50 issues were detected across the site. The most critical finding was: Outbound telemetry to Sentry may expose user data via third-party data sharing. Issues span Security, Legal, A11y, Performance categories. Persona feedback rated Visual highest (8/10) and Accessibility lowest (6/10).
Qualitative Quality
Bedlam
Category Avg
Best in Category
Pages Tested · 4 screenshots
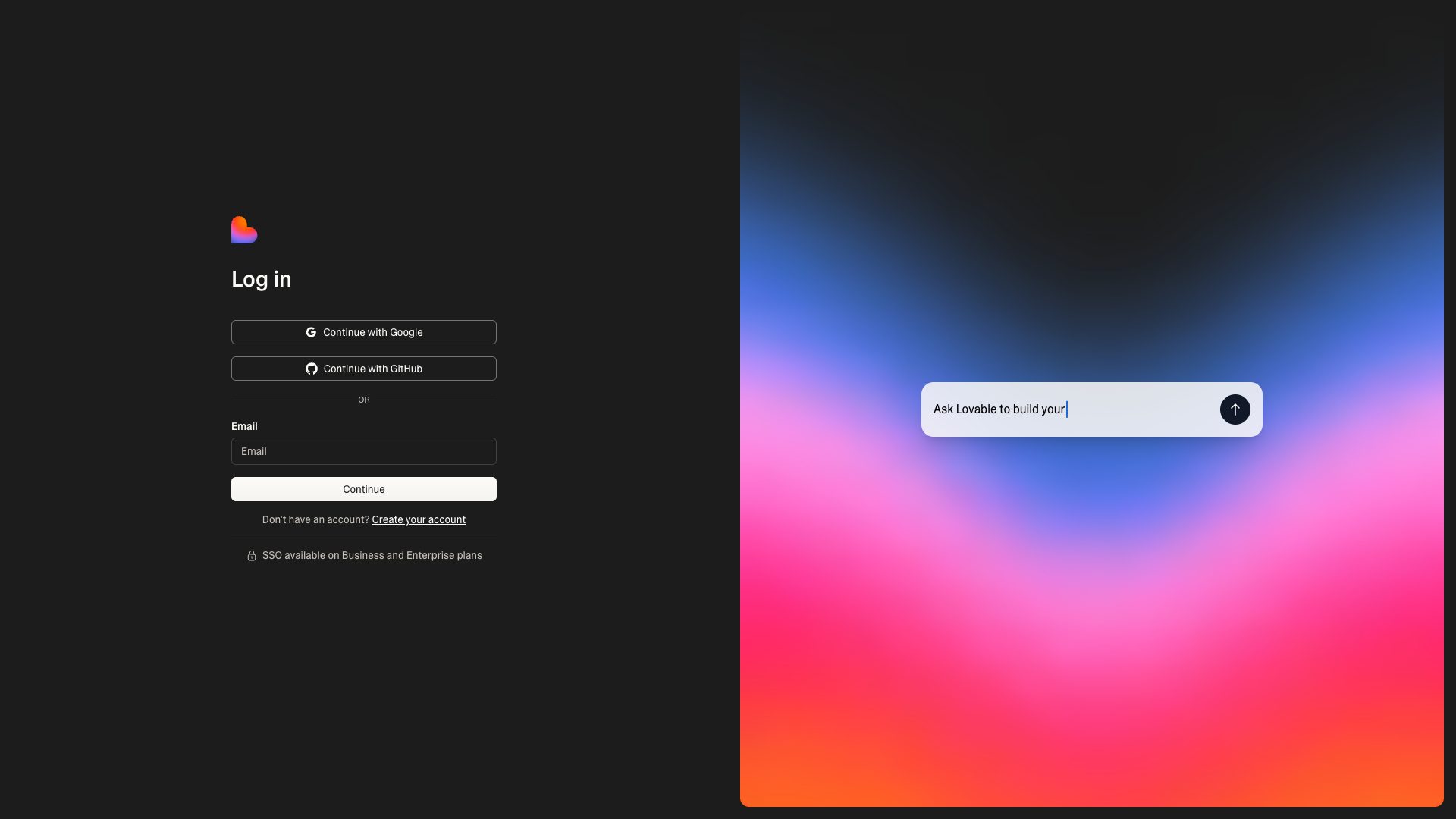
Homepage
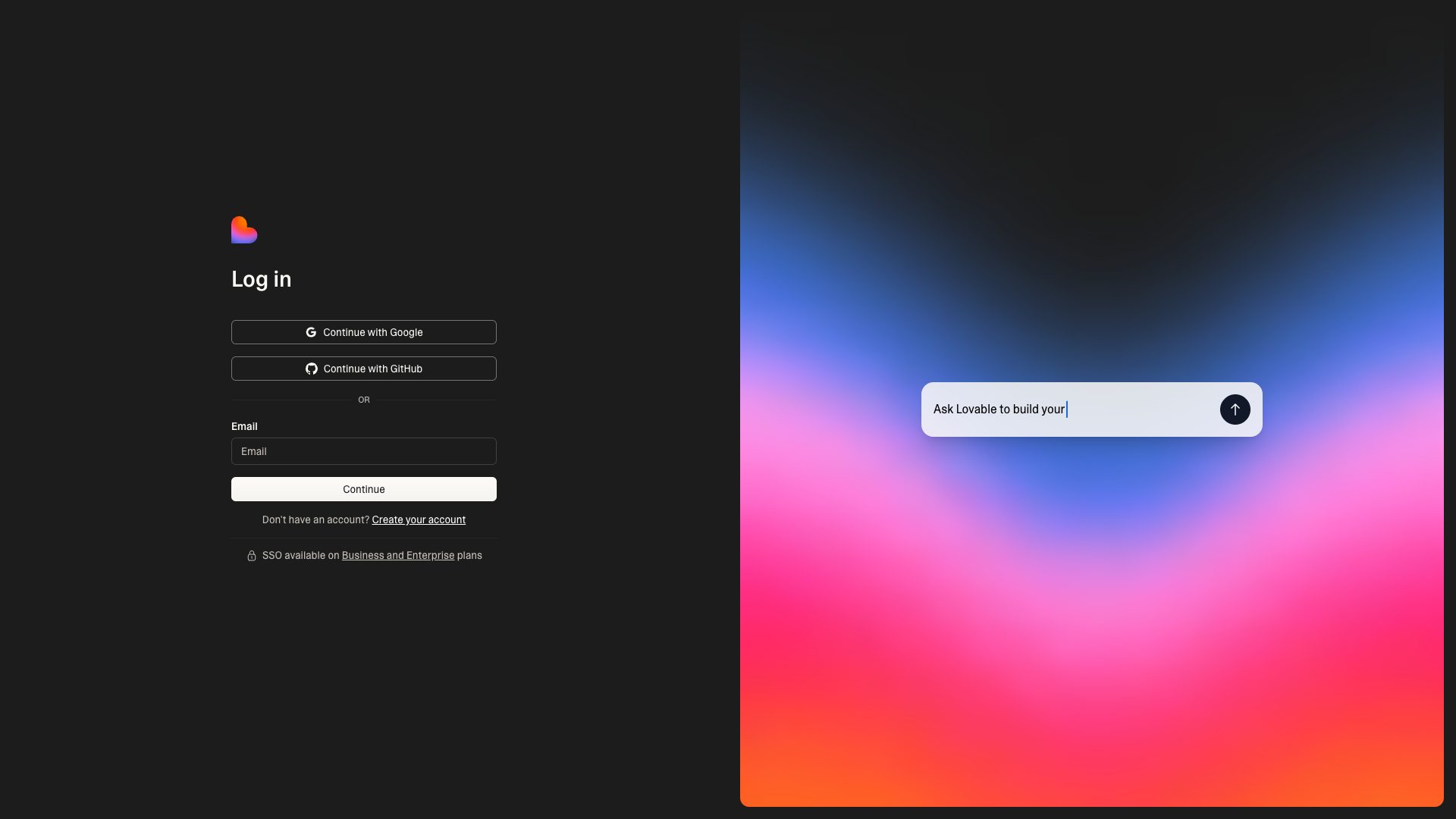
lovable.dev.products.bedlam

lovable.dev.products.bedlam

lovable.dev.products.bedlam
Detected Issues · 50 total
1
Outbound telemetry to Sentry may expose user data via third-party data sharing
CRIT P9
Prompt to Fix
In the Next.js app, ensure Sentry telemetry is privacy-preserving. Add a beforeSend hook to scrub PII from events and disable PII collection by default. Specifically: (1) remove or redact event.user.name, event.user.email, event.user.username, and any other PII fields; (2) remove sensitive data from event.request (headers cookies, authorization; and any sensitive header fields); (3) sanitize event.request.url by removing query parameters that may contain user data; (4) set sendDefaultPii: false; (5) consider limiting captured data to non-identifying metrics and enable a user consent toggle for telemetry. Example code (pseudo): import * as Sentry from '@sentry/nextjs'; Sentry.init({ dsn: process.env.SENTRY_DSN, beforeSend(event){ if(event.user){ delete event.user.email; delete event.user.name; delete event.user.username; event.user = {}; } if(event.request && event.request.headers){ delete event.request.headers.cookie; delete event.request.headers.authorization; } if(event.request && event.request.url){ event.request.url = event.request.url.split('?')[0]; } return event; }, sendDefaultPii: false });
Why it's a bug
The application sends telemetry data to a third-party Sentry endpoint (o4506071217143808.ingest.us.sentry.io). This represents third-party data sharing and, depending on payload, could include PII or sensitive information. Without explicit data minimization indicators in the logs, there is a real risk that user identifiers (names, emails, session data) or contextual information could be transmitted, contravening data minimization principles and regulatory expectations. The presence of a third-party endpoint in normal operation heightens privacy risk and could erode user trust if not clearly disclosed and properly mitigated.
Why it might not be a bug
Telemetry to Sentry is a common practice for error tracking and performance monitoring; many implementations redact PII by default. If the Sentry integration is configured to minimize data exposure (e.g., without personally identifiable fields, with beforeSend redaction, and without sending cookies or auth headers), this may be acceptable. The logs show the endpoint but not the payload, so the exact risk depends on the actual data being transmitted.
Suggested Fix
Implement strict data minimization for all telemetry sent to Sentry. Redact or remove any PII from events (e.g., user.name, user.email, phone numbers, addresses) and strip sensitive headers (cookie, authorization) before sending. Disable default PII in Sentry (sendDefaultPii: false) and add a beforeSend hook to scrub event.user, event.request data, and query parameters. Consider self-hosted or opt-in telemetry with a clear privacy notice. Ensure compliance with applicable data protection regulations and document what data is collected.
Why Fix
Reducing or eliminating exposure of PII in third-party telemetry minimizes privacy risk, helps meet regulatory requirements, and preserves user trust by avoiding unintended data sharing with external services.
Route To
Security/Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.02
Credential exposure in Sentry ingest request URL (sentry_key in query string)
CRIT P9
Prompt to Fix
Actionable fix: 1) Do not expose Sentry keys in client-side request URLs. Replace direct client ingestion with a server-side proxy or ensure the DSN is loaded from environment variables without logging the full ingest URL. 2) If using a client DSN, verify that logs and analytics do not capture the full URL including the sentry_key and sentry_version. 3) Rotate the Sentry keys if leakage is suspected and restrict events to a secure domain. 4) Validate your Sentry SDK configuration to ensure events are sent through a secure channel without leaking credentials in query strings.
Why it's a bug
The network request to the Sentry ingest endpoint includes the sentry_key in the URL query string. While the key may be intended for client-side use, exposing keys in URL query parameters can lead to leakage through browser history, server logs, analytics, or referer headers. This increases the risk of credential exposure and potential misuse of the Sentry project.
Why it might not be a bug
Sentry public DSNs are designed to be embedded in client code, and the key in the query string is a common pattern for client-side error reporting. If this is a public key intended for client use, the risk is lower; however, URL exposure remains a concern and can be mitigated.
Suggested Fix
Move Sentry integration behind a backend proxy or ensure the client uses a DSN configuration that minimizes leakage (e.g., avoid logging full ingest URLs). Use environment-based DSN configuration, ensure logs do not capture full URLs with keys, rotate keys if leakage is suspected, and consider routing Sentry events through a server-side endpoint to strip sensitive query parameters before logs or proxies record them.
Why Fix
Preventing credential leakage reduces the risk of abuse, tampering with events, or triggering events from untrusted sources. It strengthens defense-in-depth for third-party error reporting.
Route To
Security Engineer
Page
Tester
Sharon · Security Networking Analyzer
Technical Evidence
Console:
Sentry ingest call observed with 'sentry_key' in the URL query stringNetwork:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.03
Exposed Sentry public DSN key in client network requests
CRIT P9
Prompt to Fix
Actionable prompt for a coding assistant: 'In the frontend/client code, replace direct client-side POST to the Sentry ingestion URL with a backend proxy. Remove any hard-coded SENTRY_KEY from client requests and load the DSN from a server-only environment variable (e.g., NEXT_PUBLIC_SENTRY_DSN should be removed from client code). Implement a backend endpoint (e.g., /api/report-error) that receives error payloads from the client and forwards them to Sentry using a server-side, restricted DSN. Add CORS that only allows requests from the trusted origin. Implement a beforeSend filter to scrub PII and limit data, and enable rate limiting on the proxy to prevent abuse. Rotate DSN/keys after deployment and add Content Security Policy and logging to detect misuse.'
Why it's a bug
The network activity includes a POST request to Sentry ingestion with a query parameter sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f. This exposes a Sentry key in client-facing traffic. Although public DSNs are intended for client-side use, exposing keys in URLs (which may appear in logs, history, or referrers) increases abuse risk such as event flooding, misuse, or targeted probing against the Sentry project.
Why it might not be a bug
Sentry public DSNs are commonly included in client code to enable error reporting, and many deployments rely on this. If the DSN in use is a standard public DSN, some teams consider this acceptable. However, best practice is to minimize exposure and use server-side reporting or proxying when possible.
Suggested Fix
1) Use a server-side proxy or backend route to forward error events to Sentry instead of calling the Sentry ingestion endpoint directly from the client. 2) If client-side reporting is required, ensure the DSN is a proper public DSN and no sensitive keys are included in the URL; do not log or expose the DSN in logs, browser history, or analytics. 3) Rotate/refresh the Sentry DSN/public key and restrict CORS/origin policies as appropriate. 4) Consider implementing a CSP and a beforeSend filter to drop or scrub sensitive data and limit which events are sent. 5) Enable origin restrictions and logging on the Sentry project to detect abuse.
Why Fix
Reducing exposure of credentials in network requests lowers the risk of abuse, spam, or misconfiguration leading to data pollution or unintended usage of the Sentry project. It also reduces chances of sensitive data leakage via logs or history.
Route To
Security Engineer
Page
Tester
Sharon · Security Networking Analyzer
Technical Evidence
Network:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.0 - Status: N/A