B86%
Quality Score
4
Pages
54
Issues
7.8
Avg Confidence
7.7
Avg Priority
19 Critical26 High8 Medium1 Low

>_ Testers.AI
AI Analysis
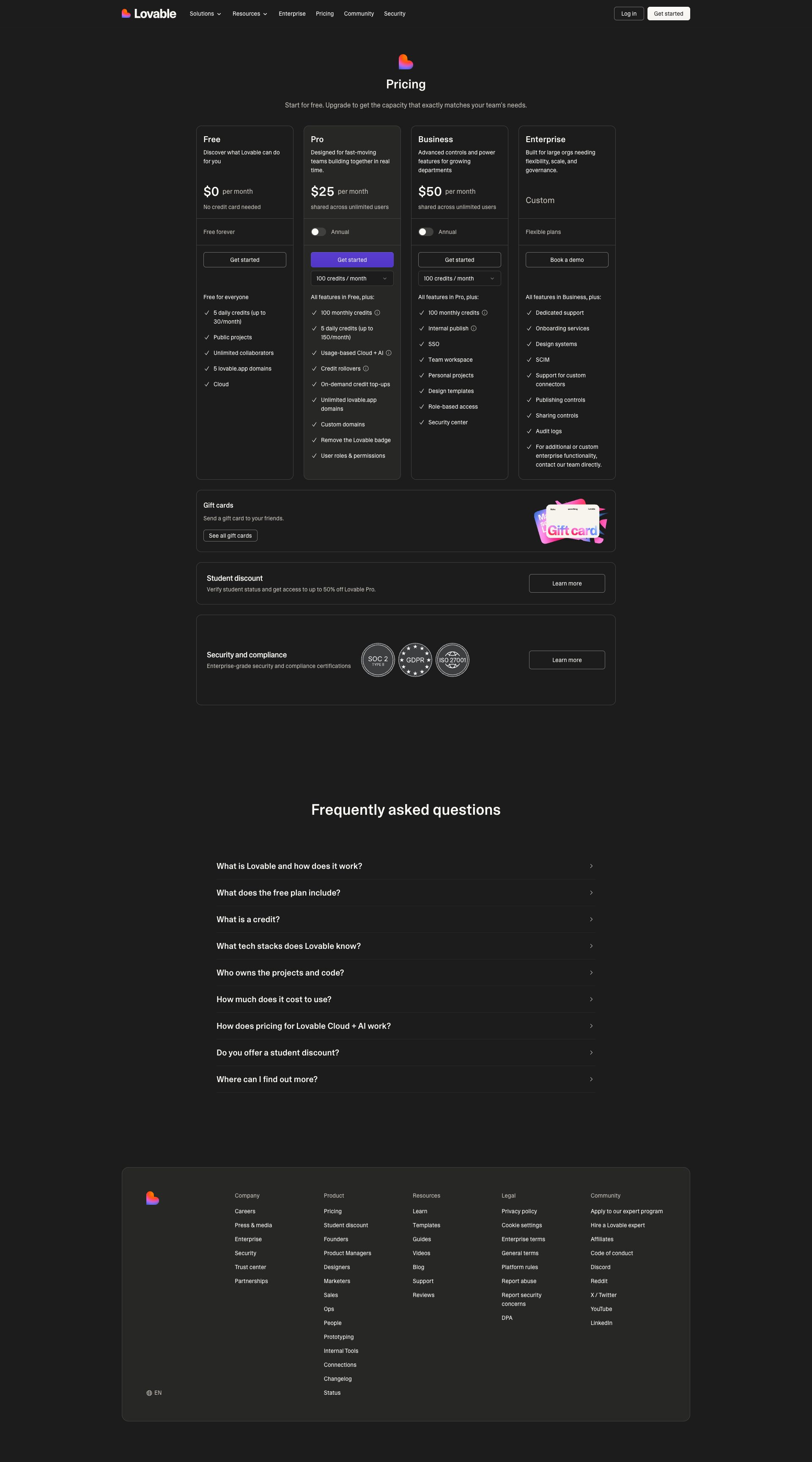
Lumoo Light Ai was tested and 54 issues were detected across the site. The most critical finding was: Third-Party Telemetry to Sentry Exposes Data Potentially Including PII. Issues span Security, Performance, A11y, Other categories. Persona feedback rated Visual highest (9/10) and Content lowest (7/10).
Qualitative Quality
Lumoo Light Ai
Category Avg
Best in Category
Pages Tested · 4 screenshots
Homepage

lovable.dev.products.lumoo

lovable.dev.products.lumoo
lovable.dev.products.lumoo
Detected Issues · 54 total
1
Third-Party Telemetry to Sentry Exposes Data Potentially Including PII
CRIT P9
Prompt to Fix
In a Next.js app, implement consent-gated, privacy-preserving Sentry integration. Before initializing Sentry, check for user consent to telemetry. If consent is given, initialize Sentry with a beforeSend hook to scrub PII (remove event.user.id, event.user.email, event.user.name, event.user.ip, and any request.cookies or sensitive headers), set sendDefaultPii to false, and minimize data collection (e.g., tracesSampleRate = 0.1). Ensure IP capture is disabled and no cookies or sensitive identifiers are transmitted. Add a clear privacy notice and a UI control to opt-in/opt-out of telemetry, and audit all third-party endpoints for disclosure and compliance.
Why it's a bug
A POST request to a Sentry ingestion endpoint indicates sending telemetry to a third-party service. Without clear user consent indicators in logs or UI, this constitutes sharing potentially sensitive or identifying data with a third party. Even if only error data is transmitted, it can include request URLs, user identifiers, IPs, and internal paths, creating regulatory risk and user privacy concerns.
Why it might not be a bug
Telemetry is common and often beneficial for debugging; if consent is clearly obtained and PII is scrubbed, data minimization practices could render this acceptable. However, the provided activity shows a direct Sentry call without visible consent controls or data minimization guarantees.
Suggested Fix
Minimize data sent to Sentry and implement explicit user consent gating for telemetry. Configure Sentry to scrub PII, disable IP capture, and avoid sending sensitive fields. Use beforeSend to filter data, set sendDefaultPii to false, and reduce tracesSampleRate. Add a user-facing privacy toggle to opt-in/opt-out of telemetry and ensure privacy policy disclosures cover third-party data sharing.
Why Fix
Protect user privacy, comply with data protection regulations, and preserve user trust by ensuring telemetry does not leak PII and is only transmitted with explicit consent.
Route To
Security/Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Console:
POST to Sentry ingestion endpoint observed; payload not shown in logs; potential PII in envelope.Network:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.02
Production debug logs leaking internal handles (JSHandle@error) in console
HIGH P8
Prompt to Fix
Remove debug-level console logs from production builds. Implement a production-ready logger with log levels and ensure internal handles or raw error objects are not printed. Review and sanitize error handling paths.
Why it's a bug
Console logs show verbose debugging messages like '[DEBUG] JSHandle@error', which can reveal internal implementation details. This is a security/observability risk and indicates insufficient log filtering for production.
Why it might not be a bug
Some debugging logs are acceptable in development, but leaking them to users or production consoles is a reliability and security concern.
Suggested Fix
Remove or gate all debug-level console logs in production builds. Replace with structured, level-controlled logging (e.g., log only at error or warn levels with sanitized messages). Ensure Sentry/telemetry logs do not expose internals.
Why Fix
Reduces security risk and avoids exposing internal debugging details to end users or attackers. Improves production instrumentation quality.
Route To
Platform/Frontend Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
[DEBUG] JSHandle@errorNetwork:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.0 - Status: N/A3
AI/LLM endpoint detected on page load causing potential privacy/perf risk
CRIT P9
Prompt to Fix
Audit all AI/LLM endpoint calls in the homepage and login flow. Remove on-load AI calls or gate them behind a user consent prompt. Implement a feature-flag to disable AI calls in production by default, and ensure only non-sensitive data is sent once consent is granted. Add telemetry to track consent and api-call failures with exponential backoff.
Why it's a bug
The network activity log clearly marks AI/LLM endpoints as detected on page load, which can cause unnecessary network traffic, potential data leakage, and slower initial rendering. This pattern often indicates AI calls are being made without explicit user consent or without deferral, harming UX and privacy expectations.
Why it might not be a bug
If the app intends to preload AI context for faster responses, it should still be clearly consented and optimized; without this, it remains a privacy concern.
Suggested Fix
Defer all AI/LLM endpoint calls until explicit user interaction or consent. Add a feature flag to disable on load, implement lazy-loading with proper rate-limiting, and ensure no sensitive data is sent until user opt-in. Document data handling in privacy/compliance notes.
Why Fix
Reducing unnecessary AI calls on load improves performance, reduces data exposure, and aligns with privacy expectations, which is critical for user trust and product reliability.
Route To
Frontend Engineer / API Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
[DEBUG] JSHandle@error
[DEBUG] JSHandle@error
⚠️ AI/LLM ENDPOINT DETECTEDNetwork:
GET https://lovable.dev/login?redirect=%2Fproducts%2Flumoo-light-ai - Status: 200
⚠️ AI/LLM ENDPOINT DETECTED