B+89%
Quality Score
4
Pages
38
Issues
8.1
Avg Confidence
8.0
Avg Priority
15 Critical19 High4 Medium

>_ Testers.AI
AI Analysis
Neurotunescopy4Privatesharing was tested and 38 issues were detected across the site. The most critical finding was: Third-Party Data Sharing via Sentry Ingestion Without Clear Consent. Issues span Security, A11y, Performance, Other categories. Persona feedback rated Visual highest (9/10) and Accessibility lowest (6/10).
Qualitative Quality
Neurotunescopy4Privatesharing
Category Avg
Best in Category
Pages Tested · 4 screenshots

Homepage

lovable.dev.products.neurotunescopy4privatesharing

lovable.dev.products.neurotunescopy4privatesharing
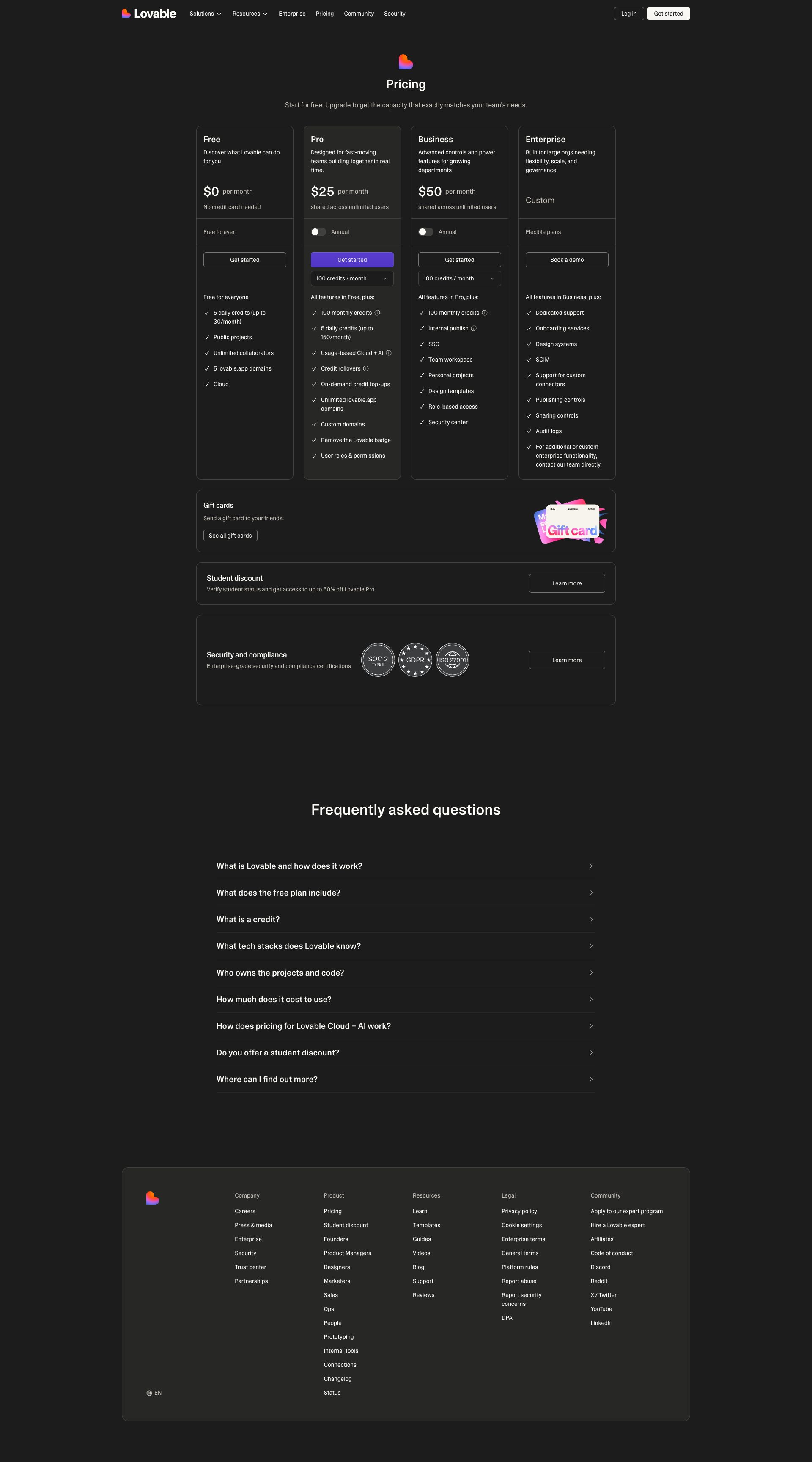
lovable.dev.products.neurotunescopy4privatesharing
Detected Issues · 38 total
1
Third-Party Data Sharing via Sentry Ingestion Without Clear Consent
CRIT P9
Prompt to Fix
In the Next.js app, the Sentry SDK is sending telemetry to a third-party endpoint. Implement explicit user consent gating for telemetry. Remove or scrub PII from all Sentry payloads by adding a beforeSend hook to strip event.user and sensitive request headers, and disable IP address or environment data where not needed. Configure sample rate to minimize data. Add privacy policy notes and consent UI. Provide a code snippet for Next.js/Sentry initialization with beforeSend, and show how to guard initialization behind a user opt-in flag.
Why it's a bug
There is a POST request to a third-party Sentry ingestion endpoint (ingest.us.sentry.io) from the application. This implies telemetry data about the user and environment is being transmitted to a third party. Without explicit user consent indicators or disclosure in the privacy policy, this constitutes undisclosed data sharing and potential PII exposure.
Why it might not be a bug
Telemetry to Sentry is common in modern apps; if the app provides a clear privacy disclosure and user consent for analytics and error reporting, this may be allowed. The log does not show the payload, so data minimization is possible, but the absence of a visible consent flow is a concern.
Suggested Fix
1) Introduce explicit user consent workflow for telemetry that gates all non-essential data collection. 2) Scrub PII from all Sentry payloads (use beforeSend in Sentry config to remove event.user, event.request.headers, and any personal fields). 3) Configure Sentry to minimize data (lower tracesSampleRate, apply data scrub rules, disable sending of IP addresses if not required). 4) Ensure privacy policy clearly documents third-party data sharing and provides an opt-in/opt-out mechanism. 5) Consider deferring or locally capturing errors until consent is given, or use a privacy-friendly alternative for non-production environments.
Why Fix
Reducing exposure of user data to third parties improves regulatory compliance (GDPR/CCPA) and user trust, and mitigates risk of sensitive information leakage through telemetry payloads.
Route To
Frontend Engineer / Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Console:
Sentry telemetry POST detected to a third-party ingestion endpoint; no visible consent flow in logsNetwork:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs/10.28.02
Exposed Sentry key in URL query parameters
CRIT P9
Prompt to Fix
Actionable fix: In the frontend codebase (e.g., Next.js app), remove any hard-coded or dynamically constructed Sentry ingest URLs that place the DSN/key in the query string. Replace with a standard Sentry initialization that reads the DSN from an environment variable (e.g., NEXT_PUBLIC_SENTRY_DSN) and passes it to Sentry.init. Example patch:
- In config: // next.config.js or runtime config export const publicRuntimeConfig = { SENTRY_DSN: process.env.NEXT_PUBLIC_SENTRY_DSN };
- In code (e.g., _app.tsx or equivalent): import * as Sentry from '@sentry/nextjs';
Sentry.init({ dsn: process.env.NEXT_PUBLIC_SENTRY_DSN, tracesSampleRate: 1.0, environment: process.env.NODE_ENV || 'production' });
- Remove any references to a URL containing sentry_key in query parameters from the client code.
- Rebuild and redeploy, and verify via network logs that requests to Sentry no longer include sentry_key in the URL query string.
- Optionally add a quick security review to ensure no other credentials are exposed in URLs or logs.
Why it's a bug
The network activity shows a POST to Sentry's ingest endpoint with a sentry_key parameter included in the URL query string. While Sentry public DSN components are not strictly secret, placing credentials in the URL can leak through browser history, referer headers, logs, analytics, and analytics tooling. This increases the risk of unintended exposure and misuse of monitoring data.
Why it might not be a bug
Sentry DSNs contain public components and are designed to identify the project; exposure of the public DSN itself typically does not grant unauthorized access. However, best practices strongly discourage placing any credentials or keys in URL query strings due to potential leakage across logs and intermediaries.
Suggested Fix
Refactor frontend Sentry initialization to avoid including credentials/keys in URLs. Move the DSN/key into a secure configuration sourced from environment variables and loaded at runtime. Example: use NEXT_PUBLIC_SENTRY_DSN (or a server-side config exposed securely) and initialize Sentry with Sentry.init({ dsn: process.env.NEXT_PUBLIC_SENTRY_DSN, tracesSampleRate: 1.0, environment: process.env.NODE_ENV || 'production' }). Ensure no code constructs or transmits the Sentry ingest URL with the key in a query string.
Why Fix
Preventing exposure of Sentry keys in URLs reduces risk of credential leakage via logs, browser history, or referer headers, and aligns with secure coding practices for third-party monitoring services.
Route To
Frontend Engineer
Page
Tester
Sharon · Security Networking Analyzer
Technical Evidence
Console:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.0 - Status: N/ANetwork:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.0 - Status: N/A3
On-load AI/LLM endpoint detected causing potential data leakage
CRIT P9
Prompt to Fix
In the frontend codebase (Next.js/React), identify any client-side calls to AI/LLM endpoints that occur on page load. Remove or lazy-load these calls, gating AI interactions behind explicit user consent or by routing them through secured server-side endpoints. Remove production debug logs indicating AI endpoints and ensure prompts/data sent to AI services are sanitized and consent-gated.
Why it's a bug
Console/network logs show 'AI/LLM ENDPOINT DETECTED' markers and evidence of AI endpoint usage in the client bundle. This implies AI calls could be triggered on page load, potentially sending user data to third-party AI services without explicit consent, risking privacy and compliance issues.
Why it might not be a bug
If AI features are strictly server-side or behind explicit user consent, client-side indicators alone may be benign; the screenshot only shows detection markers and does not prove data exfiltration. However, presence of such markers in production code is worrisome.
Suggested Fix
Remove on-load AI/LLM calls from the client bundle or defer them behind explicit user action. Move AI interactions to server-side routes with proper authentication and data handling. Remove debug 'AI endpoint detected' logs from production builds and centralize AI endpoints via environment config with proper consent prompts.
Why Fix
Prevents unintended data exposure, reduces performance issues, and aligns with privacy expectations and regulatory requirements.
Route To
Frontend/Full-Stack Engineer (Security-focused)
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
⚠️ AI/LLM ENDPOINT DETECTEDNetwork:
N/A (AI endpoint usage detected via console; exact network calls not visible in screenshot)