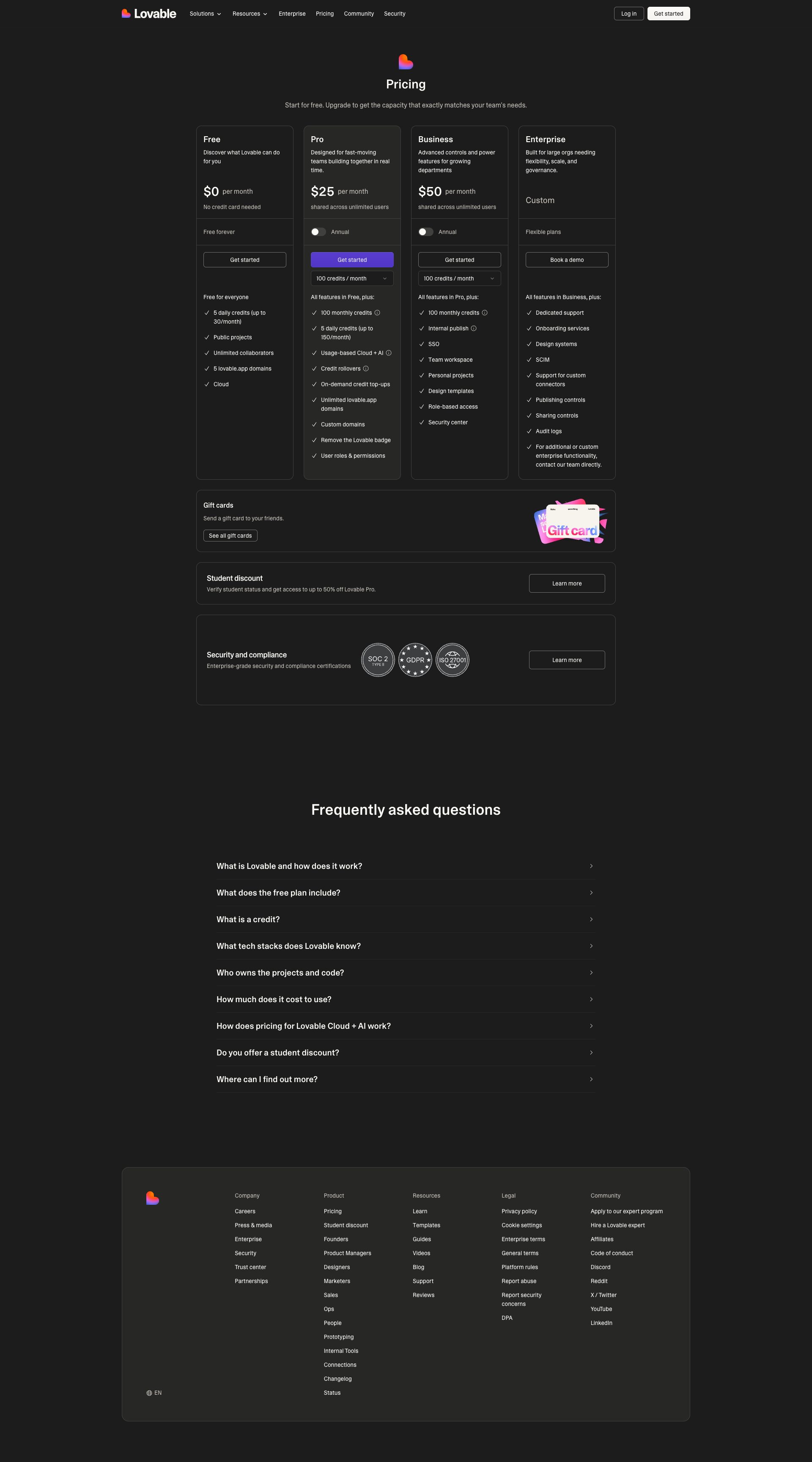
B85%
Quality Score
4
Pages
43
Issues
8.0
Avg Confidence
7.8
Avg Priority
15 Critical21 High7 Medium

>_ Testers.AI
AI Analysis
Voisley was tested and 43 issues were detected across the site. The most critical finding was: Outbound Sentry telemetry to third-party domain without explicit consent indicator. Issues span Performance, A11y, Other, Content categories. Persona feedback rated Visual highest (8/10) and Accessibility lowest (4/10).
Qualitative Quality
Voisley
Category Avg
Best in Category
Pages Tested · 4 screenshots

Homepage

lovable.dev.products.voisley

lovable.dev.products.voisley
lovable.dev.products.voisley
Detected Issues · 43 total
1
Outbound Sentry telemetry to third-party domain without explicit consent indicator
CRIT P9
Prompt to Fix
Actionable fix for privacy issue: In the frontend, remove or gate the Sentry ingestion behind a user consent flow. Update initialization to minimize data sent: disable default PII collection, enable IP address anonymization, and implement a beforeSend filter to scrub sensitive fields. Add a visible privacy notice and an option in user settings to opt-out of telemetry. If telemetry is enabled, ensure only non-identifying data (e.g., error type, message without user identifiers) is transmitted. Document the data practices in the privacy policy.
Why it's a bug
There is a network request from the frontend to a third-party Sentry ingestion endpoint (ingest.us.sentry.io). This implies telemetry data (error/diagnostic information) is being sent to a third-party service. Without an explicit consent indicator visible in the flow or clearly minimizable data, this poses a privacy risk due to potential exposure of user- and device-related data and cross-site tracking concerns. The request itself is to a third-party domain, increasing the chance of data sharing beyond the primary site.
Why it might not be a bug
Many apps rely on Sentry for error monitoring; if user consent is obtained via privacy policy or a consent banner and telemetry is minimized, this would not be a bug. Proper configuration can ensure only non-identifying telemetry is sent or that users opt-in/opt-out explicitly.
Suggested Fix
Configure Sentry integration to minimize data collection: disable sending of personally identifiable information (PII), enable IP anonymization, and ensure default PII is not captured. Add a clear consent toggle for telemetry in the UI and respect user choice. Use a beforeSend hook or equivalent to scrub data, and consider sending only non-identifying error data in production. If feasible, provide an opt-out option or gate telemetry behind a privacy-consent banner.
Why Fix
Reducing third-party data sharing and potential PII exposure improves user privacy, aligns with data minimization principles, and helps maintain regulatory compliance while preserving essential error monitoring through configurable, consent-aware telemetry.
Route To
Privacy Engineer / Frontend Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Network:
POST https://o4506071217143808.ingest.us.sentry.io/api/4506071220944896/envelope/?sentry_version=7&sentry_key=58ff8fddcbe1303f19bc19fbfed46f0f&sentry_client=sentry.javascript.nextjs%2F10.28.02
Excessive network requests and large JS bundles
CRIT P9
Prompt to Fix
Run a bundle analysis (e.g., webpack-bundle-analyzer). Identify large or unused modules and enable dynamic imports for non-critical code. Remove dead code, optimize dependencies, and consider splitting large vendor bundles. Apply preloading/prefetching for critical routes and ensure CSS/JS are loaded non-blocking where appropriate.
Why it's a bug
The page lists around 131 network requests with numerous JavaScript chunks being loaded. This can lead to longer load times, heavier parsing/compile time, and worse Time To Interactive on slower connections.
Why it might not be a bug
Some frameworks split code into chunks by design; however, there is likely room to optimize by reducing unused code and improving bundling strategy.
Suggested Fix
Audit with a bundle analyzer; implement code-splitting and dynamic imports for heavy modules; remove or lazy-load unused dependencies; combine or optimize CSS where possible; ensure critical JS is loaded ASAP and non-critical chunks are deferred; enable HTTP/2/Quic on the server/CDN to multiplex requests efficiently.
Why Fix
Smaller, more targeted bundles, and fewer total requests improve LCP, TTI, and FID, especially on mobile networks, and reduce CPU work during parsing/execution.
Route To
Frontend / Build Engineer
Page
Tester
Tariq · Performance Specialist
Technical Evidence
Console:
[DEBUG] JSHandle@errorNetwork:
GET https://lovable.dev/_next/static/chunks/44ba6248b61f6e8d.js?dpl=dc5974b1d3364da313fd2b41e61f010a3
AI/LLM endpoint calls on initial render
CRIT P9
Prompt to Fix
Action: Move all AI/LLM endpoint calls from initial render to after explicit user action. Do not load or call AI endpoints for fonts or UI assets during page load. Implement a feature-flag 'enableAIEndpoints' checked before any LLM interaction; require user consent for AI features; lazy-load assets without invoking AI.
Why it's a bug
Console logs show '⚠️ AI/LLM ENDPOINT DETECTED' and multiple LLM-related endpoints are invoked during page load, which can leak prompts, impact performance, and surprise users.
Why it might not be a bug
If the app intentionally uses LLM calls on load for dynamic UI, it should be clearly disclosed and behind a user-consent/feature-flag. Without consent, this is a privacy and UX risk.
Suggested Fix
Delay or lazy-load all AI/LLM calls until the user explicitly interacts with the feature (e.g., clicking 'Ask Lovable' or enabling a settings option). Remove or conditionally gate font/asset calls that route through AI endpoints. Add a consent/flag system and ensure no sensitive data is sent in initial requests.
Why Fix
Reduces unexpected network usage, improves page load performance, and mitigates potential data leakage from prompts or AI requests.
Route To
Frontend Engineer / Security & Privacy Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
⚠️ AI/LLM ENDPOINT DETECTEDNetwork:
GET https://lovable.dev/fonts/CameraPlainVariable-c48bd243.woff2 - Status: 200; GET https://lovable.dev/fonts/CameraPlainVariableRegularItalic-8524cd9a.woff2 - Status: 200