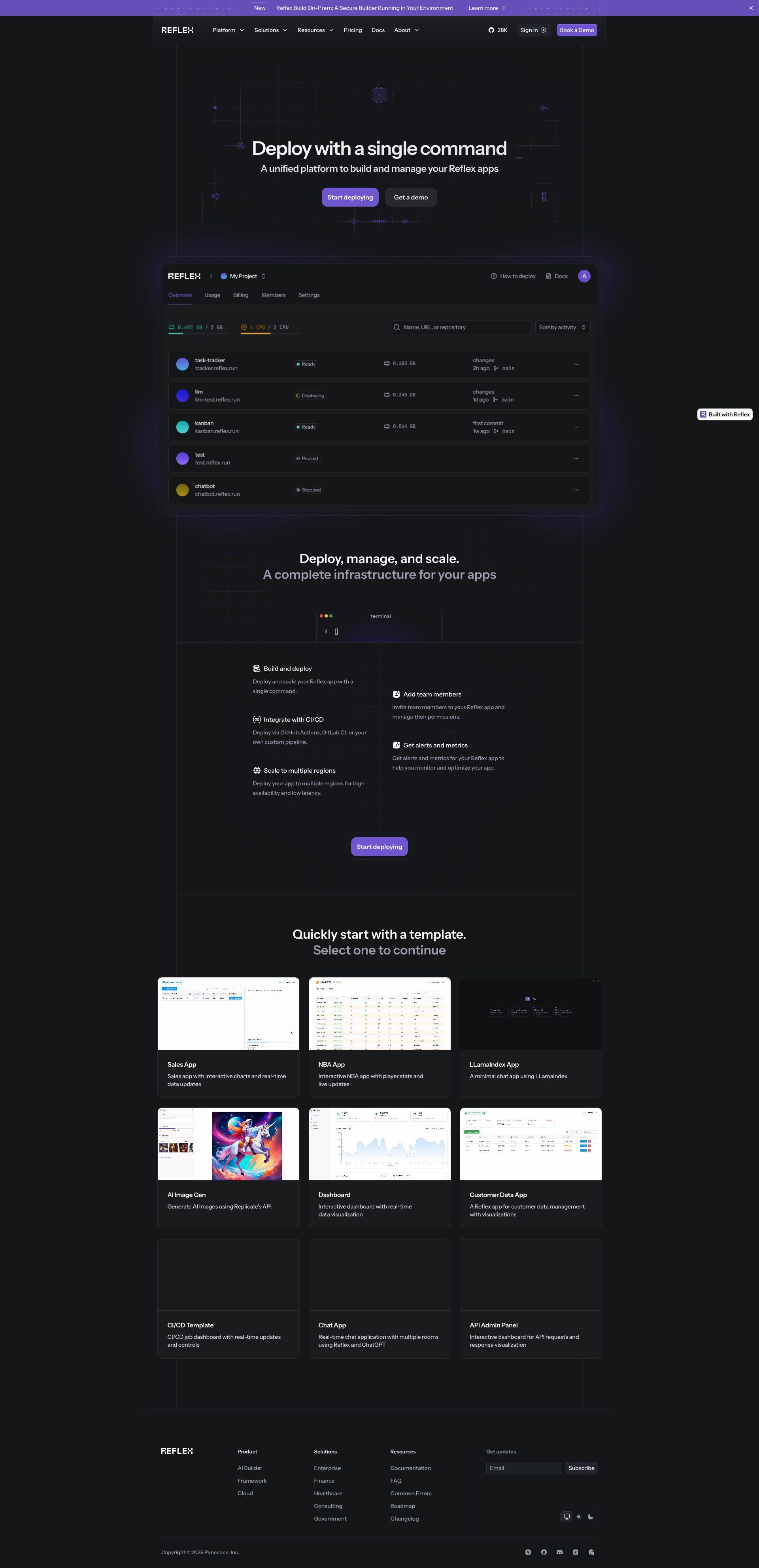
B83%
Quality Score
7
Pages
101
Issues
7.9
Avg Confidence
7.9
Avg Priority
45 Critical38 High18 Medium

>_ Testers.AI
AI Analysis
Reflex was tested and 101 issues were detected across the site. The most critical finding was: Potential Tracking Pixel detected on reflex assets CDN (framework_pixel.svg). Issues span Security, A11y, Performance, Other categories. Persona feedback rated Visual highest (6/10) and Accessibility lowest (5/10).
Qualitative Quality
Reflex
Category Avg
Best in Category
Pages Tested · 7 screenshots
Homepage
reflex.dev
reflex.dev
reflex.dev
reflex.dev
reflex.dev
reflex.dev
Detected Issues · 101 total
1
Potential Tracking Pixel detected on reflex assets CDN (framework_pixel.svg)
CRIT P9
Prompt to Fix
In the frontend code, remove or gate the framework_pixel.svg tracking pixel call behind an explicit user consent prompt. If analytics are still required, switch to a first-party analytics endpoint on reflex.dev, ensure no personal data or identifiers are transmitted via the URL or headers, hash or anonymize user identifiers, and ensure the asset is only loaded after consent is given. Add a privacy notice and respect Do Not Track.
Why it's a bug
The request to https://web.reflex-assets.dev/common/light/framework_pixel.svg appears to function as a tracking pixel. It loads a tiny image and can be used to detect page views, user presence, and cross-site activity without explicit user consent. This constitutes potential cross-site tracking and data collection.
Why it might not be a bug
If this asset is a first-party resource on a domain under explicit control with a clear consent mechanism, it could be legitimate analytics. However, there is no visible consent prompt or privacy notice associated with this asset in the provided context.
Suggested Fix
Gate the tracking pixel behind explicit user consent. If analytics are required, replace with a privacy-preserving, consented solution hosted on a first-party domain. Remove or replace third-party tracking pixels, and ensure Do Not Track and opt-out preferences are respected. Consider setting a stricter Referrer-Policy and removing any tracking identifiers from requests.
Why Fix
Tracking pixels can enable cross-site profiling and data collection without user knowledge. Fixing this reduces privacy risk and aligns with data minimization principles.
Route To
Privacy Engineer
Page
Tester
Pete · Privacy Networking Analyzer
Technical Evidence
Console:
⚠️ POTENTIAL ISSUE: Tracking request detectedNetwork:
GET https://web.reflex-assets.dev/common/light/framework_pixel.svg2
AI endpoint detected on page load – potential unintended client-side LLM usage
CRIT P9
Prompt to Fix
Identify any client-side calls or references to AI/LLM endpoints that run on initial page load. Remove or defer these calls behind a user action or consent. If server-side rendering is required, move the logic to the server, ensure no prompts/data are sent from the client without consent, and implement proper error handling and backoff.
Why it's a bug
Console shows '⚠️ AI/LLM ENDPOINT DETECTED' and related logs, which implies that AI/LLM endpoints may be invoked or referenced from the client on initial paint. This can lead to data leakage, increased load times, and lack of user consent for GenAI usage.
Why it might not be a bug
If the detection is a development-time diagnostic, it should be gated behind a feature flag or removed in production. Without explicit context, treat as a high-risk potential issue.
Suggested Fix
- Move all AI/LLM calls behind explicit user actions or consent prompts.- Consider moving calls to a secure server-side proxy and remove hard-coded client-side endpoints.- Implement proper error handling, backoff, and rate limiting; avoid logging sensitive data.
Why Fix
Reduces risk of data leakage, improves performance, and ensures GenAI usage is intentional and auditable.
Route To
Frontend Security/Platform Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
"⚠️ AI/LLM ENDPOINT DETECTED"3
Production debug logs reveal AI endpoint usage
HIGH P8
Prompt to Fix
Remove production console logs that reveal internal AI endpoint usage. Implement proper log levels and only log such events in development. Sanitize messages and avoid exposing endpoint domains.
Why it's a bug
Console contains '⚠️ AI/LLM ENDPOINT DETECTED' messages, which could leak internal AI infrastructure details to end users or visitors. Debug logs in production are a security/privacy risk.
Why it might not be a bug
If this is a development build, it may be acceptable; in production, it would be a vulnerability.
Suggested Fix
Remove or gate all AI-endpoint detection logs from production builds, add log level guards, and ensure messages do not reveal endpoint details. Sanitize messages and consider privacy disclosures for AI usage.
Why Fix
Prevents leakage of internal endpoints and reduces attack surface.
Route To
Security Engineer / Frontend Engineer
Page
Tester
Jason · GenAI Code Analyzer
Technical Evidence
Console:
⚠️ AI/LLM ENDPOINT DETECTEDNetwork:
N/A (log message indicates endpoint usage rather than a direct network call).