
Intel Capital scored B (83%) with 45 issues, ranking #45 of 47 VC sites. That's 22 more than the 22.7 category average (4th percentile).
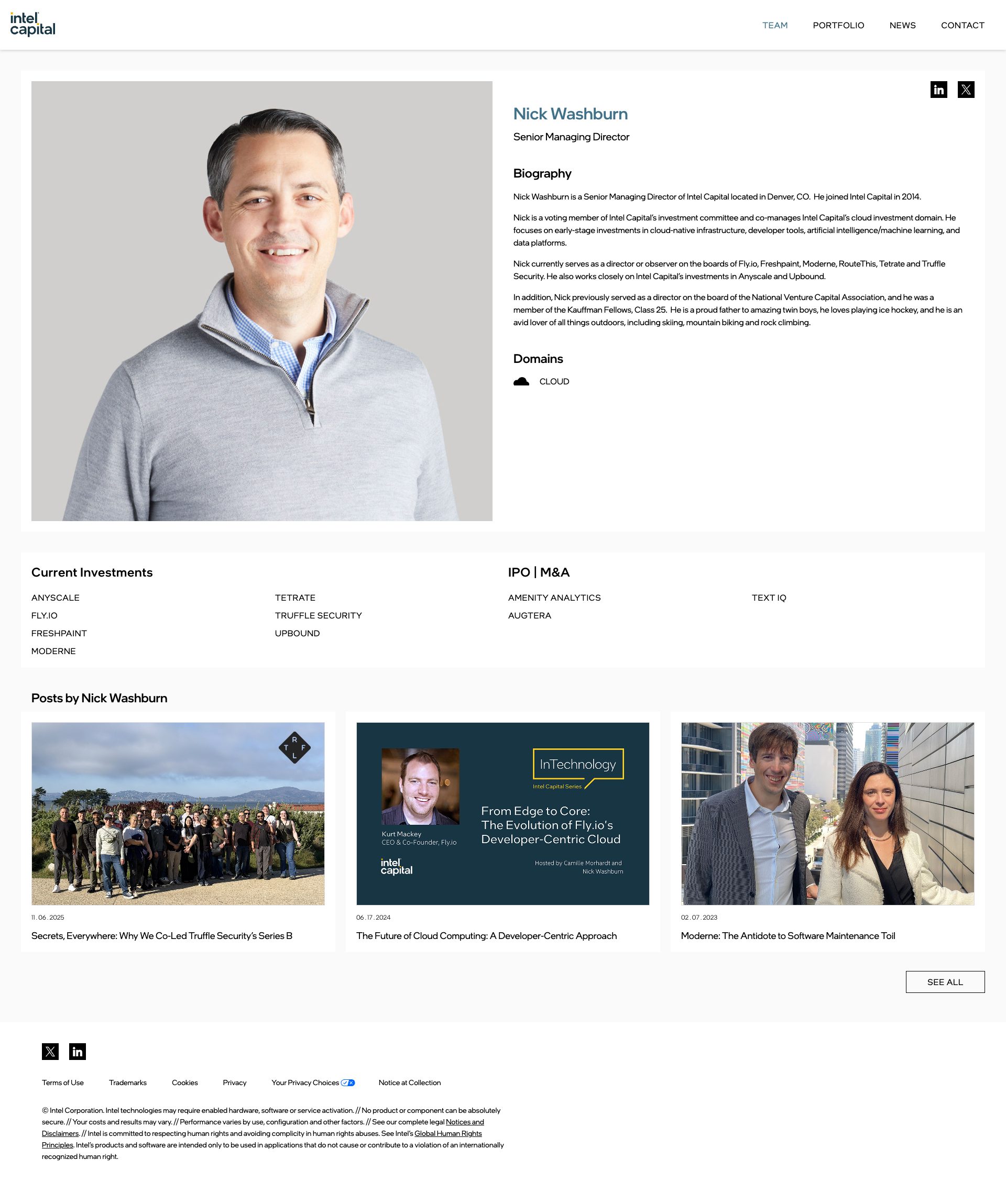
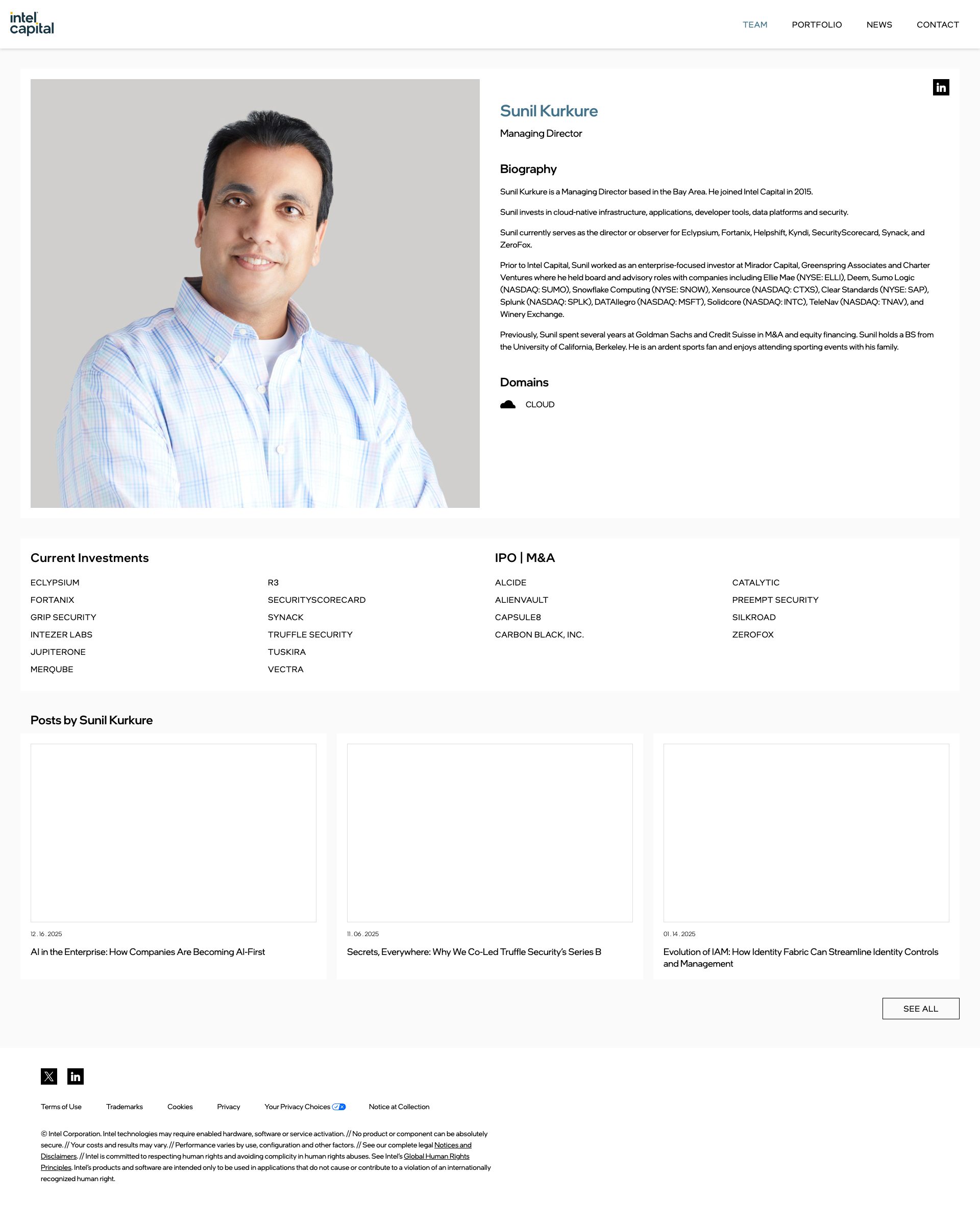
Top issues to fix immediately: "Potential XSS vulnerability in user-generated content display" — Ensure all user-generated content and dynamic data is properly HTML-escaped and sanitized server-side before rendering; "Potential XSS vulnerability in news article content display" — Implement Content Security Policy (CSP) headers, ensure all user-generated content is properly escaped/sanitized usin...; "Missing alt text on team member profile images" — Add descriptive alt text to each profile image following the pattern 'Portrait of [Name], [Job Title]' or similar.
Weakest area — accessibility (5/10): Image-heavy design with overlaid text may present contrast and screen reader challenges.
Quick wins: Add a prominent above-the-fold value proposition or mission statement to clarify Intel Capital's purpose immediately. Improve text contrast on image overlays and ensure all images have descriptive alt text for screen readers.












 Sharon · Security Tester
Sharon · Security Tester<div class='content'>, dynamic content rendering areasNot visible in screenshotNot visible in screenshotThe C' | Chief Client Officer, course modules list, testimonials section Sharon · Security Tester
Sharon · Security Tester<div class='article-content'>, <p> tags, potentially unchecked innerHTML assignmentsCheck for CSP violation warnings or sanitization errors in consoleContent delivery and sanitization endpointsArticle content in main news section with multiple formatted paragraphs Sharon · Security Tester
Sharon · Security Tester<a> tags in Related News sidebar, href attributes pointing to external domainsCheck for warnings about cross-origin links without proper attributesExternal link redirect endpoints and verification servicesRelated News section with sambanova, eliyan, upscale ai company links