
Next scored B (84%) with 141 issues across 7 tested pages, ranking #14 of 20 UK retail sites. That's 11 more than the 130.2 category average (35th percentile).
Top issues to fix immediately: "Multiple DNS Resolution Failures - Critical Network Issues" — 1) Identify which exact URLs are failing to resolve by adding more specific logging to the network requests; "Exposed Google Maps API Key in Client-Side Request" — Implement a server-side proxy endpoint that accepts map requests from the client and forwards them to Google Maps API...; "Exposed Google Maps API Key in Network Request" — 1) Immediately rotate and revoke the exposed API key in Google Cloud Console.
Weakest area — accessibility (5/10): Images lack visible alt text indicators, color contrast in some sections may be insufficient, and interactive elements lack cle...
Quick wins: Enhance accessibility by adding clear alt text to all images, improving color contrast ratios, and implementing visible.... Improve navigation hierarchy by making main category links more prominent in the header or adding a persistent....
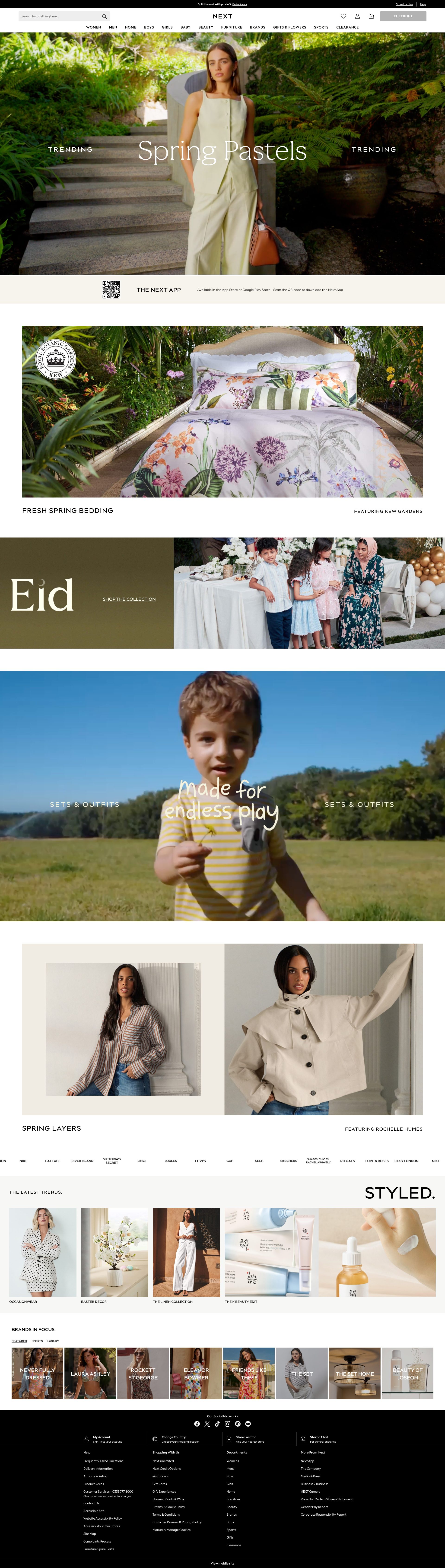


 Sharon · Security Networking Analyzer
Sharon · Security Networking AnalyzerGoogle Maps API Key visible in Network tabGET https://maps.googleapis.com/maps/api/js?v=3&key=AIzaSyBp7ukJ04Ku2k9OjqRQP0aw2S1uzW-JqTM&callback=googleMapsApiLoadCallback Jason · GenAI Code Analyzer
Jason · GenAI Code AnalyzerN/A - visible in network requestGET https://maps.googleapis.com/maps/api/js?v=3&key=AIzaSyBp7ukJ04Ku2k9OjqRQP0aw2S1uzW-JqTM&callback=googleMapsApiLoadCallback - Status: N/A Pete · Privacy Networking Analyzer
Pete · Privacy Networking AnalyzerGoogle Maps API initializationGET https://maps.googleapis.com/maps/api/js?v=3&key=AIzaSyBp7ukJ04Ku2k9OjqRQP0aw2S1uzW-JqTM&callback=googleMapsApiLoadCallback